CompTIA Sec+ | Microsoft MTA Security: Most Common Application/Service Attacks Part 1
“Richard Clarke, a former counter-terrorism expert for the United Government, once said, “If you spend more on coffee than on IT security, you will be hacked. What’s more, you deserve to be hacked”. While the latter is a tad harsh (we wouldn’t wish a cyber attack on anyone!), the former is certainly true.”
If you don’t protect yourself and your business from cybercrime, it’s only a matter of time before you’ll be the victim of an attack. According to a Statistics, In 2018, the number of data breaches in the United States amounted to 1,244 with over 446.5 million records exposed. (statista, n.d.)
The best way to protect yourself is to know about the different types of cyber attacks. Then you can use that information and take steps to make your networks secure.
Here are some Common Application/Service Attacks that you need to know.
DDoS
What is a DDos Attack?
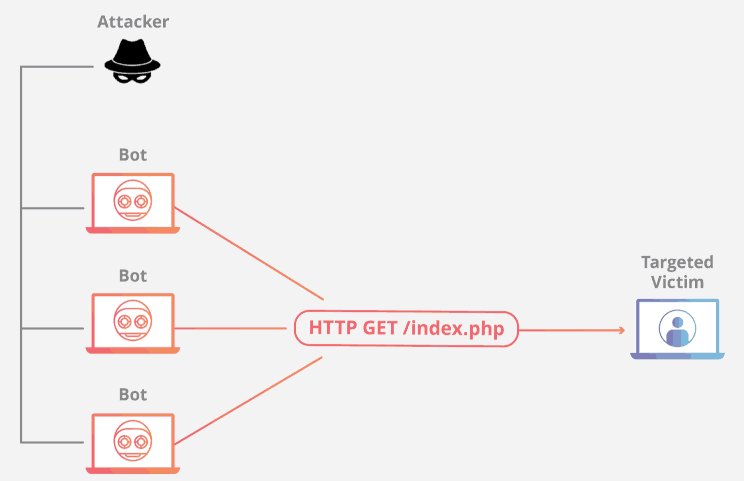
A distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt normal traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic. DDoS attacks achieve effectiveness by utilizing multiple compromised computer systems as sources of attack traffic. Exploited machines can include computers and other networked resources such as IoT devices. From a high level, a DDoS attack is like a traffic jam clogging up with highway, preventing regular traffic from arriving at its desired destination (Cloudflare, n.d.).
Example of a DDoS attack: Application Layer Attacks
Sometimes referred to as a layer 7 DDoS attack (in reference to the 7th layer of the OSI model), the goal of these attacks is to exhaust the resources of the target. The attacks target the layer where web pages are generated on the server and delivered in response to HTTP requests. A single HTTP request is cheap to execute on the client side, and can be expensive for the target server to respond to as the server often must load multiple files and run database queries in order to create a web page. Layer 7 attacks are difficult to defend as the traffic can be difficult to flag as malicious (Cloudflare, n.d.).
Buffer Overflow
What is a Buffer Overflow?
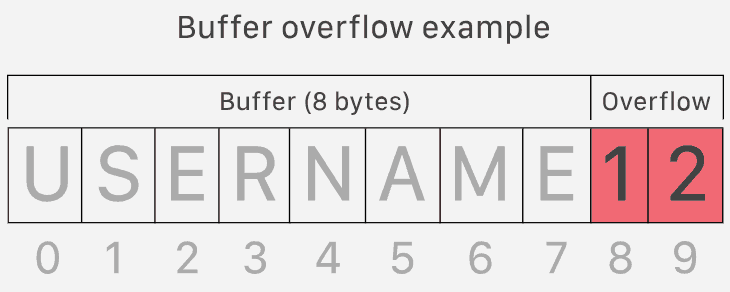
Applications set aside areas of memory, or buffers, for use as storage, frequently setting aside a finite amount of memory for a buffer. A buffer overflow exists when an application attempts to store more data than can fit in a fixed-size buffer. Buffer overflow attacks occur when an intruder is able to send data in excess of a fixed-size application buffer and the application does not check to ensure this doesn’t happen. By overflowing a buffer with executable code, an intruder can cause an application to perform unexpected and often malicious actions using the same privileges the application has been granted (Symantec Corporation, n.d.).
What is a Buffer Overflow Attack?
An attack that works by exploiting a known bug in one of the applications running on a server. This then causes the application to overlay system areas, such as the system stack, thus allowing the attacker to gain administrative rights. In most cases, this gives the attacker complete control over the system. Also called stack overflow (Symantec Corporation, n.d.).
Cross-site Scripting
What is a Cross-site Scripting?
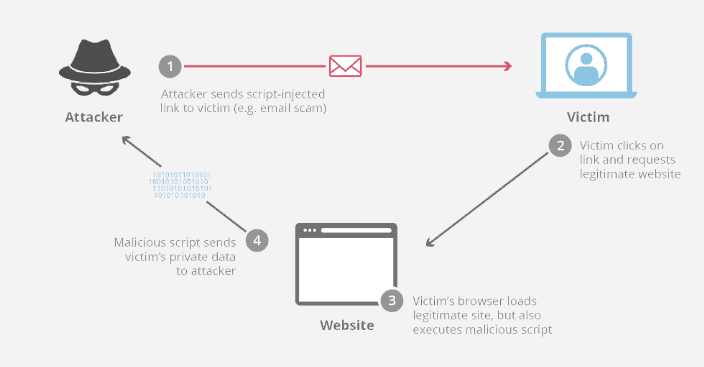
Cross-site scripting is what happens when an attacker takes advantage of a vulnerability in a webpage to inject their own code. That code can steal user information such as credentials, session cookies, and other sensitive data, and can even live persistently on a site to attack multiple users.
A XSS attack is unique because these vulnerabilities don’t target the website or web app they exploit—it’s only an attack vector. XSS uses scripts that are executed on a user’s machine; these scripts are called client-side scripts. The vast majority of these are coded in JavaScript or HTML, though there are other languages that can be used for client-side scripts (Vigliarolo, 2018).
What is an example of cross-site scripting?
One useful example of cross-site scripting attacks is commonly seen on websites that have unvalidated comment forums. In this case, an attacker will post a comment consisting of executable code wrapped in ‘’ tags. These tags tell a web browser to interpret everything between the tags as JavaScript code. Once that comment is on the page, when any other user loads that website, the malicious code between the script tags will be executed by their web browser, and they will become a victim of the attack.
Cross-Site Request Forgery
What is Cross-Site Request Forgery?
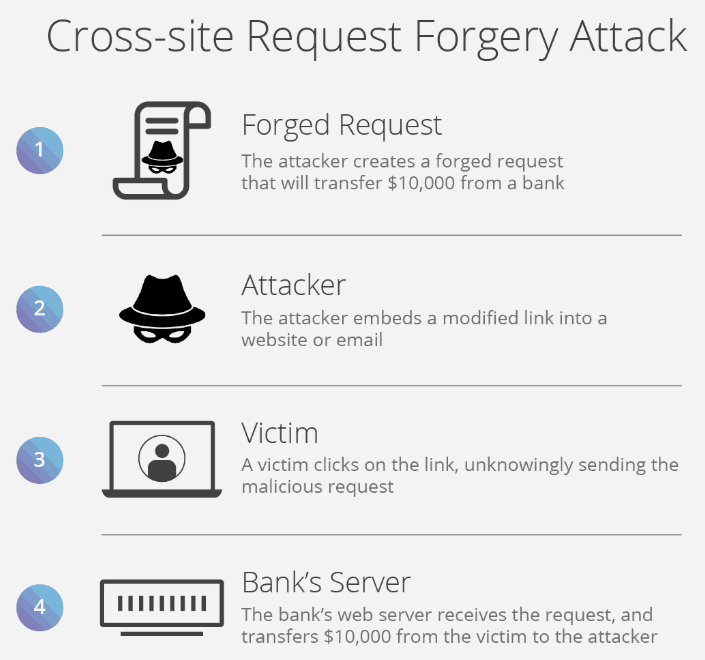
Cross-Site Request Forgery, often abbreviated as CSRF, is a possible attack that can occur when a malicious website, blog, email message, instant message, or web application causes a user’s web browser to perform an undesired action on a trusted site at which the user is currently authenticated. The impact of a CSRF attack is determined by the capabilities exposed within the vulnerable application. CSRF attacks are, on the most basic level, used by an attacker to make a target system perform any available and malicious function via the target’s browser without knowledge of the target user. This function usually is not known by the victim until after it has occurred as well.
A CSRF vulnerability can give an attacker the ability to force an authenticated, logged-in user to perform an important action without their consent or knowledge. It is the digital equivalent to someone forging the signature of a victim on an important document. It is in fact more effective, because the attacker leaves no trace of evidence behind. This is because the forged request contains all of the information and comes from the same IP address as a real request from the victim. This means that any application that allows a user to send or update data is a possible target for an attacker.
One important thing to remember is that for CSRF to work, the victim has to be logged in the targeted site. While this may feel like an impedance to the attacker, many websites let the user choose to “keep me logged in”. This greatly increases the size of the timeframe in which a forgery can be made (Barracuda, n.d.).
Examples of CSRF.
The most common goal of a CSRF is theft—either data theft, identity theft, or financial theft. Some common uses of CSRF include:
- Transfer money from one bank account to another. Your online session at your bank becomes compromised, and treats this like a legitimate request and sends $1000 from your account to Mallory’s account. All evidence suggests you legitimately made this transaction from your logged-in browser.
- Use a content management system to add/delete content from a website. If the victim is an administrative user, the entire website would be under the attacker’s control.
- Change a user’s password. If a victim is logged into their account, the attacker can simply forge a request for an email change. Once this goes through, If the attacker can forge a password reset request, the attacker could subsequently gain full control of the victim’s account.
- Add items to a user’s shopping basket or change the delivery address of an order. Many websites have a “my account” page or other similar pages that stores a user’s information, and often allows a user to change their address or adjust their shopping cart. With CSRF, an attacker can adjust this information, and to the website, it will look as if the victim was the originator of all changes .
DNS Poisoning
What is DNS poisoning?
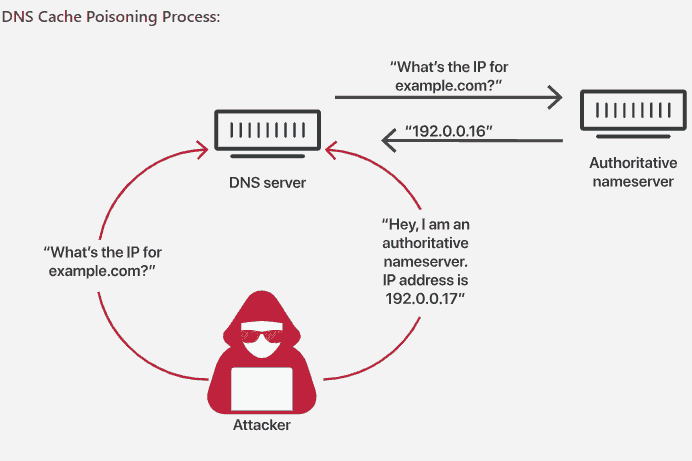
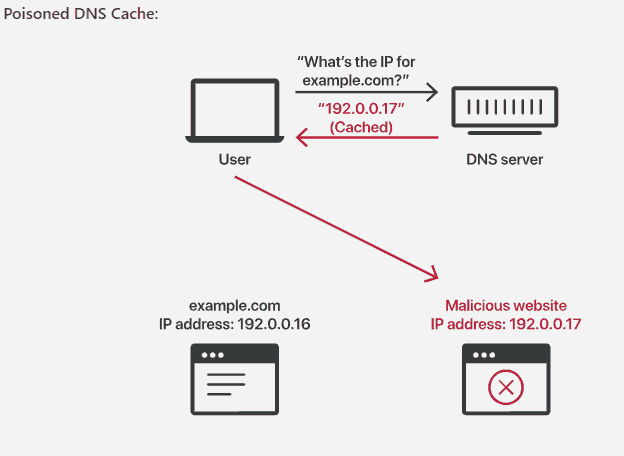
DNS cache poisoning, also known as DNS spoofing, is a type of attack that exploits vulnerabilities in the domain name system (DNS) to divert Internet traffic away from legitimate servers and towards fake ones. (HOFFMAN, n.d.)
This kind of attack is often categorized as a “pharming” attack and it creates several problems. First, users think they are at a familiar site, but they aren’t. Unlike with a “phishing” attack where an alert user can spot a suspicious URL, in this case the URL is legitimate. Remember, the browser resolves the address of the domain automatically so there is no intervention of any kind on the part of the users and, since nothing unusual has happened, they have no reason to be suspicious.
Another problem is that hundreds or even thousands of users can be redirected if an attacker successfully inserts a single fake entry into a caching server. The scale of the problem is amplified by the popularity of the domain being requested. Under these circumstances, even a moderately experienced hacker can cause a lot of trouble, obtaining passwords and other valuable or sensitive information.
It is possible to attack e-mail systems in a similar way. Rather than inserting a fake record for a Web server into a DNS caching server, the attacker inserts a fake record for a mail server, thereby redirecting corporate e-mail to a server they control.
Want to learn more about our CompTIA Security+ Certification Courses? Click here.
References
Barracuda. (n.d.). What is CSRF? Retrieved from www.barracuda.com/: https://www.barracuda.com/glossary/csrf
Cloudflare. (n.d.). What is a DDoS Attacks? Retrieved from Cloudflare.com: https://www.cloudflare.com/learning/ddos/what-is-a-ddos-attack/
HOFFMAN, C. (n.d.). What is DNS Cache Poisoning? Retrieved from www.howtogeek.com: https://www.howtogeek.com/161808/htg-explains-what-is-dns-cache-poisoning/
statista. (n.d.). Cyber crime: number of breaches and records exposed 2005-2018. Retrieved from www.statista.com: https://www.statista.com/statistics/273550/data-breaches-recorded-in-the-united-states-by-number-of-breaches-and-records-exposed/
Symantec Corporation. (n.d.). Buffer Overflow. Retrieved from us.norton.com: https://us.norton.com/online-threats/glossary/b/buffer-overflow.html
Vigliarolo, B. (2018, December 3). Cross-site scripting attacks: A cheat sheet. Retrieved from https://www.techrepublic.com: https://www.techrepublic.com/article/cross-site-scripting-attacks-a-cheat-sheet/
Product categories
Are you looking to break into the exciting field of cybersecurity? Join our 5-day CompTIA Security+ Bootcamp Training and build your cybersecurity knowledge and skills.
Or
Become a certified ethical hacker! Our 5-day CEH Bootcamp is unlike other strictly theoretical training, you will be immersed in interactive sessions with hands-on labs after each topic. You can explore your newly gained knowledge right away in your classroom by pentesting, hacking and securing your own systems. Learn more






