Two-Factor or Multi-Factor Authentication (2FA or MFA)
CompTIA Security+ Objective 4.1 and CompTIA Network+ Objective 4.2
What is two-factor or multi-factor authentication (2FA or MFA)?
Multifactor authentication ensures that a user is who they say they are. The more factors are used to determine the identity of a person, the greater the reliability of the authenticity.
Typical MFA scenarios include:
1) Swiping a card and entering a PIN.
2) Logging into a website and being requested to enter an additional one-time password (OTP) that the website’s authentication server sends to the requester’s phone or email address.
3) Downloading a VPN client with a valid digital certificate and logging into the VPN before being granted access to a network.
4) Swiping a card, scanning a fingerprint and answering a security question.
5) Attaching a USB hardware token to a desktop that generates a one-time passcode and using the one-time passcode to log into a VPN client.
Background
One of the largest problems with traditional user ID and password login is the need to maintain a password database. Whether encrypted or not, if the database is captured it provides an attacker with a source to verify his guesses at speeds limited only by his hardware resources. Given enough time, a captured password database will fall.
As processing speeds of CPUs have increased, brute force attacks have become a real threat. Further developments like GPGPU password cracking, rainbow tables and now the Quantum computers have provided greater advantages for the attackers. GPGPU cracking, for example, can produce more than 500,000,000 passwords per second, even on lower end gaming hardware. Depending on the particular software, rainbow tables can be used to crack 14-character alphanumeric passwords in about 160 seconds. Recently, a paper released by Google’s researchers that was briefly posted on a Nasa’s website before being removed, claimed that their processor was able to perform a calculation in three minutes and 20 seconds that would take today’s most advanced classical computer, known as Summit, approximately 10,000 years. With these capabilities, a password database alone doesn’t stand a chance against such methods when it is a real target of interest.
In the past, MFA systems typically relied upon two-factor authentication. Increasingly, vendors are using the label “multifactor” to describe any authentication scheme that requires more than one identity credential.
Authentication factors
An authentication factor is a category of credential used for identity verification. For MFA, each additional factor is intended to increase the assurance that an entity involved in some kind of communication or requesting access to some system is who, or what, they are declared to be. The five most common categories are often described as something you know (the knowledge factor), something you have (the possession factor), something you are (the inherence factor), somewhere you are (location factor) and something you do (Time factors).
Something you know (The knowledge factor)
Accessing any account requires credentials by registering a unique username and password. Cellphone PINs and the answers to secret questions also fall under this category. Creating a strong password is still recommended.
Strong Password – Consisting of at least 8 characters that contain a combination of letters, numbers, and symbols if allowed. Case-sensitive letters along with passwords that do not contain words that can be found in a dictionary.
However, even strong passwords we use today lack credibility in the security world, thus introducing two-factor authentication (2FA) or multi-factor authentication (MFA).
Something you have (The possession factor)
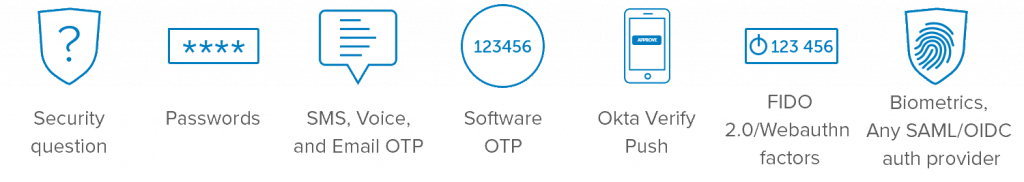
Anything a user must have in their possession in order to log in, such as a security token, a one-time password (OTP) token, a key fob, an employee ID card or a phone’s SIM card. For mobile authentication, a smartphone often provides the possession factor, in conjunction with an OTP app.
Something you are (The inherence factor)
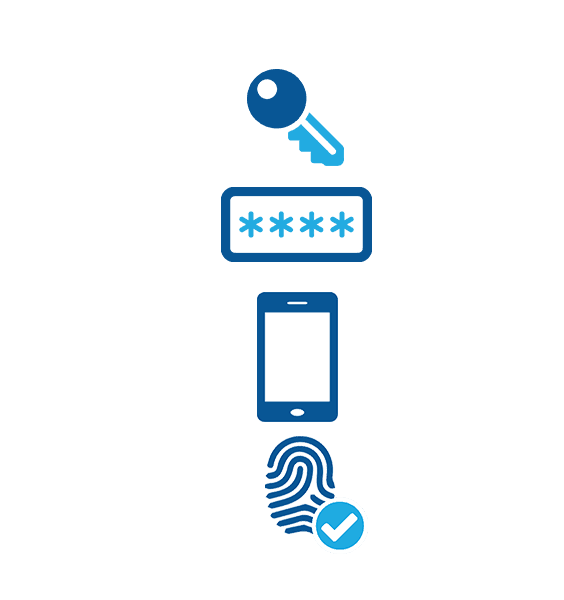
Any biological traits the user has that are confirmed for login. This category includes the scope of biometric authentication methods such as retina scans, iris scans fingerprint scans, finger vein scans, facial recognition, voice recognition, hand geometry, even earlobe geometry.
Somewhere you are (The location factor)
The user’s current location is often suggested as a fourth factor for authentication. Again, the ubiquity of smartphones can help ease the authentication burden here: Users typically carry their phones and most smartphones have a GPS device, enabling reasonable surety confirmation of the login location. Often times, an email service will send you notifications about a log-in from a certain location that is not typical with the user’s usual location —the MFA tool may require the user to enter a code texted to the user’s phone.
Something you do (The Time factor)
Often called Adaptive Authentication, this type of MFA takes context into account to flag logins that are out of the ordinary. When a person tries to authenticate in an unusual context, Adaptive MFA may tighten security by requesting additional credentials. For example, if a user is logging in from a cafe late at night—and this is not typical for that user—the MFA tool may require the user to enter a code texted to the user’s phone.
MFA is an effective way to provide enhanced security. Traditional usernames and passwords can be stolen, and they’ve become increasingly more vulnerable to brute force attacks. MFA creates multiple layers of security to help increase the confidence that the user requesting access is actually who they claim to be. With MFA, a cybercriminal may steal one credential but will be thwarted by having to verify identity in a different manner.
Sources:
NIST
Independent
Are you looking to break into the exciting field of cybersecurity? Join our 5-day CompTIA Security+ Bootcamp and build your cybersecurity knowledge and skills.
Check out our network+ bootcamp as well and become an expert in managing, maintaining, troubleshooting, installing and configuring basic computer networks.






