Penetration Testing Vs Vulnerability Scanning
Security+ Objectives 1.4
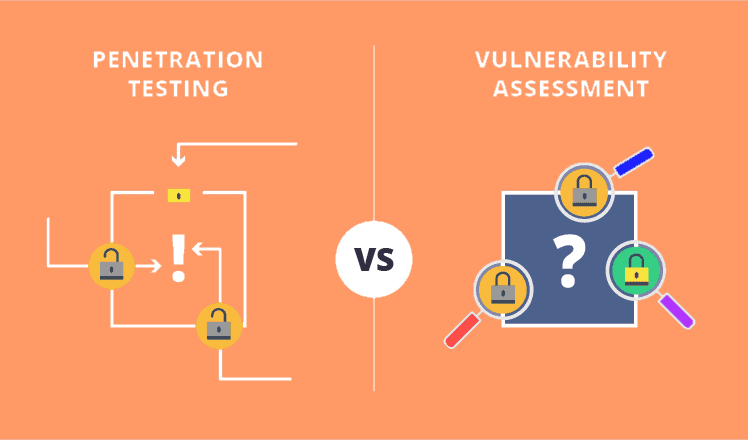
Penetration Testing & Vulnerability Scanning, What's the Difference?
What is Penetration Testing?
Penetration testing is a way to “stress test” your IT infrastructure security. Penetration techniques are used to evaluate the safety and security of the network in a controlled manner. Operating systems, services, applications, and even the behavior of the end user is assessed to validate existing defense mechanisms and the efficacy of end-user security policies. The goal is to gain unauthorized access through exploitation which can be used to emulate the intent of a malicious hacker.
What is Vulnerability Scanning?
vulnerability scanning, or VA, is the process of identifying threats and vulnerabilities on a target by using automated vulnerability scanners. This sometimes includes a range of manual testing with additional tools to further evaluate the security of applications or networks and to verify vulnerabilities discovered by the scanning applications.
Objectives
For Pentest
A pentest is often initiated by various scenarios which can include (but are not limited to) application launches, major network/application changes or updates, compliance regulations or a breach/leak from a targeted attack.
Due to the varied reasons for conducting a pentest, the objectives can often differ greatly as well. Industry experts generally divide penetration testing into three categories: black box testing, white box testing, and gray box testing. The categories correspond to different types of attacks or cybersecurity threats. For more information.
Generally, the end goal of an ethical hacker is to gain unauthorized access to a target by means of exploiting uncovered vulnerabilities from the scanning and enumeration phase. Your organization, however, may have an alternative end goal in mind due to the requirements for conducting the pentest in the first place.
Some of the objectives and occasions for conducting a pentest are as follows:
Application launches: A pentest may be conducted as part of the software development life cycle (SDLC) process to uncover existing vulnerabilities which should be resolved before the launch. The main objective is to help save time and money by discovering and fixing vulnerabilities before an application is deployed into production and open to end users or potentially malicious hackers.
Major network/application change or update: Pentests are often scheduled on an annual, bi-annual or quarterly basis to maintain best security practices and stay on top of any major changes which could potentially uncover new vulnerabilities. A pentest may be initialized on this cycle or when a major change in a network or application occurs.
Vulnerability management program: The landscape of attacks is evolving at a rapid pace which usually eclipses the awareness and knowledge that organizations maintain with regards to their security posture. In order to attempt to stay on top of this, it is imperative to continuously assess the applications and infrastructure on a regular or at least semi-regular basis.
There is a famous quote in the infosec community by John Chambers (former CEO of Cisco) which explains the need for this continuous maintenance: “There are only two types of companies: Those that have been hacked, and those that don’t know they have been hacked.”
Compliance regulations: A pentest can be conducted with the objective of meeting certain compliance standards which have requirements to perform penetration tests at certain periods. Depending on the type of data organizations process or store, they may be required to abide by different compliance regulations (e.g. PCI DSS, HIPAA, Sarbanes-Oxley). Some of these regulations require a pentest to address the risks and potential security exposure an organization may have to aid in the protection of this regulated data.
After a breach or leak: This is quite possibly the worst reason to conduct a pentest but is also very common unfortunately. After having already been breached and having confidential data being exposed to the public, an organization may panic and immediately hire a vendor to conduct a pentest to prevent a similar leak from happening again in the future. The objective here is to uncover any additionally existing vulnerabilities and holes an organization may have since they are already well aware that flaws exist in the first place. This is a reactive approach used to prevent similar breaches in the future.
For Vulnerability Scanning
The objectives of a vulnerability scanning can be somewhat different compared to that of a penetration test.
Where a pentest can sometimes be more responsive or mandatory for various reasons, a vulnerability scanning can be more cyclical to be proactive at discovering vulnerabilities and to perform patching as part of an ongoing vulnerability management program or when new vulnerabilities are released. Pentests are also included as part of a vulnerability management program, however, these will be much less frequent than vulnerability scannings within the actual program.
In this case, VSs should be a frequent and ongoing process to continuously monitor and identify weaknesses in an organization and reduce the attack surface.
There are also many cases where a VS is performed after a leak occurs, when a new prominent vulnerability comes to light, or if a change in a network or application takes place.
objectives of these are as follows:
New vulnerability released: When a new headline vulnerability hits the market, many companies and executives panic immediately. Calls are made to their VS teams or vendors to conduct an scanning ASAP to hunt for this new vulnerability in their organization. Recent examples of this include EternalBlue, KRACK, Meltdown/Spectre and Heartbleed.
The scannings take place shortly after word gets out that another one of these vulnerabilities have come to light, and the objective here is to determine whether there is any presence of such a vulnerability in an organization.
Network/application change: This falls somewhat into a vulnerability management program but will remain separate since not all organizations have or maintain such a program. Anytime a major change, update or migration takes place (have you moved buildings recently?), this should be an immediate trigger to re-scan and assess the environment to find weaknesses which may have been created due to these changes. Maybe something was missed while setting up the network and an extra access point or server was left behind open to the external network. It’s things like this which happen frequently and are often forgotten.
Vulnerability management program: Application security and patch management are a continuous process within a good vulnerability management program. This will include vulnerability scanning of applications and networks to identify weaknesses and patches that should be applied. The entire program should be cyclical which will require vulnerability scannings on a monthly, quarterly or annually basis, depending on the targets, to stay on top of new vulnerabilities and exposures in an organization.
After a breach or leak: This fits in the same category as execution of a pentest after a breach or leak. A vulnerability scanning should be initiated to uncover potential flaws which still exist within the organization to prevent another attack from occurring. If you’ve made the headlines due to the attack, maybe your internal sensitive information has been passed around in some dark hacker forums. This information, or just the fact that there are/were open vulnerabilities, can be enough to trigger additional attacks by hackers. Staying on top of all attack surfaces is paramount in keeping this exposure to a minimum and minimizing the chances occurrence in the near future.
Who Usually Performs a Pentest/VS?
Hackers! White hat ones, of course (we hope). A pentest team can have an extremely Varied background as far as education and experience goes. But no matter what, they all have one important thing in common – a passion for security and great curiosity to find and break things. It’s this passion that unites all pentesters and makes them great at their jobs.
Conclusion
Before starting the process of hiring a vendor for a security scanning, it is crucial to know the differences between a pentest and a vulnerability scanning to be sure that your organization is getting what it wants and needs based your business requirements. A pentest can have a drastically higher price tag than a VS, but if you only require a small VS, then it isn’t worth it to pay out all that cash for a pentest.
Once you have a solid understanding of the main differences, you can make the right decision for your organization and better determine the scope of the engagement. In the end, you will be left with the type of test and report you were looking for and the required patching that lies ahead.
Categories
Sources: Solarwinds, pentest-standard script
Are you looking to break into the exciting field of cybersecurity? Join our 5-day CompTIA Security+ Bootcamp Training and build your cybersecurity knowledge and skills.
Or
Become a certified ethical hacker! Our 5-day CEH Bootcamp is unlike other strictly theoretical training, you will be immersed in interactive sessions with hands-on labs after each topic. You can explore your newly gained knowledge right away in your classroom by pentesting, hacking and securing your own systems. Learn more






