Protocols and Encryption
CompTIA A+ Core 2 -Chap 2.2 | Security+ Chap 6.3
Protocols and Encryption
WEP
WEP – (wired equivalent privacy) is a standard network protocol that adds security to Wi-Fi and other 802.11 wireless networks. WEP was designed to give wireless networks the same level of privacy protection as a comparable wired network, but technical flaws greatly limit its usefulness. Newer, stronger protection standards have replaced WEP as the default for most modern networks.
How WEP Works
WEP uses a data encryption scheme that is based on a combination of user- and system-generated key values. The original implementations of WEP supported encryption keys of 40 bits plus 24 additional bits of system-generated data, leading to keys of 64 bits in total length. To increase protection, these encryption methods were later extended to support longer keys, including 104-bit (128 bits of total data), 128-bit (152 bits total), and 232-bit (256 bits total) variations.
When deployed over a Wi-Fi connection, WEP encrypts the data stream using these keys so that it is no longer human-readable but can be processed by receiving devices. The keys are not sent over the network but are stored on the wireless network adapter or in the Windows registry.
Why WEP Is Not Recommended for General Use
WEP was introduced in 1999. Within a few years, several security researchers discovered flaws in its design. The “24 additional bits of system-generated data” is technically known as the initialization vector and proved to be a critical protocol flaw. With simple and readily available tools, a hacker can determine the WEP key and use it to break into an active Wi-Fi network.
Vendor-specific enhancements to WEP such as WEP+ and dynamic WEP attempted to patch some of the shortcomings of WEP, but these technologies have proved unworkable.
Replacements for WEP
WPA replaced WEP in 2004, and WPA2 replaced WPA. Although running a network with WEP enabled is better than running with no wireless encryption protection at all, the difference is negligible from a security perspective.
WPA
WPA – WiFi Protected Access, is a Wi-Fi security technology was created in 2003 and was developed in response to the weaknesses of Wired Equivalent Privacy standards. It improves upon WEP’s authentication and encryption features.
As the WiFi Alliance made this transition to a more advanced protocol, they had to keep some of the same elements of WEP so older devices would still be compatible. Unfortunately, this means vulnerabilities, such as the WiFi Protected Setup feature which can be hacked relatively easily, are still present in the updated version of WPA.
What Is WPA-PSK?
WPA Pre-Shared Key is a variation of WPA designed for home networks. It’s a simplified but still powerful form of WPA.
Similar to WEP, a static key or passphrase is set, but WPA-PSK uses TKIP. WPA-PSK automatically changes the keys at preset intervals to make it difficult for hackers to find and exploit them.
WPA2
WPA2 – Wi-Fi Protected Access 2 is a network security technology commonly used on Wi-Fi wireless networks. It’s an upgrade from the original WPA technology, which was designed as a replacement for the older and much less secure WEP. WPA2 is used on all certified Wi-Fi hardware since 2006 and is based on the IEEE 802.11i technology standard for data encryption.
WPA2 Limitations
The only notable vulnerability of WPA2 is that once someone has access to the network, they can attack other devices connected to the network. This is an issue if a company has an internal threat, such as an unhappy employee, who hacks into the other devices on the company’s network.
Using WPA2 decreases the performance of network connections due to the extra processing load of encryption and decryption. The performance impact of WPA2 is usually negligible, especially when compared with the increased security risk of using WPA or WEP, or no encryption at all.
AES vs. TKIP for Wireless Encryption
The main difference with WPA2 is that it uses the Advanced Encryption Standard (AES) instead of TKIP. AES is able to secure top-secret government information, so it’s a good option for keeping a personal device or company WiFi safe.
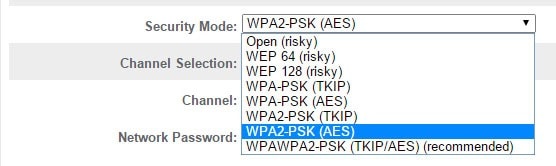
Many home routers let administrators choose from among these possible combinations:
WPA with TKIP (WPA-TKIP): This is the default choice for old routers that don’t support WPA2.
WPA with AES (WPA-AES): AES was first introduced before the WPA2 standard was completed, although few clients supported this mode.
WPA2 with AES (WPA2-AES): This is the default choice for newer routers and the recommended option for networks where all clients support AES.
WPA2 with AES and TKIP (WPA2-AES/TKIP): Routers need to enable both modes if any clients do not support AES. All WPA2 capable clients support AES, but most WPA clients do not.
WPA3
As vulnerabilities are recognized, advancements are made. In 2018, the WiFi Alliance introduced WPA3. This new version will have, “new features to simplify WiFi security, enable more robust authentication and deliver increased cryptographic strength for highly sensitive data markets.”
WPA3 support availability
This isn’t to say that you can buy the new hardware and get up and running on WPA3 immediately. The first generation of support for WPA3 in client devices is just rolling out. Android 10 has support, but it is still in beta (as of September 2019), and there is no official release date. The same goes for Apple, which has released WPA3 support in iOS 13. The latest builds of Windows 10 have support for WPA3-SAE, but there’s an important short-term qualifier on Windows support: Windows may support it, but the device driver for the network hardware must also. This will take time, and there may be old devices that don’t get support. There is no word from Apple on support in the Mac, but if iOS is supporting WPA3, Mac support is likely not far off.
With all those caveats, nascent, incomplete support for WPA3 is much more valuable than universal and mature support for WPA2, especially for new purchases and especially on consumer configurations, which are the ones you would use in your home or any small business. As client support starts to increase, it is critical that network infrastructure already support it.
While support for WPA3 is growing, routers and access points will be able to offer older clients a fallback to the WPA2 PSK and Open methods, but those users will be vulnerable while the WPA3 users on the same network will be protected.
Even though operating system support for WPA3 is only beginning to be released, the imperative for WPA3 is clear: It is demonstrably more secure than WPA2 and not having it will, before too long, make your wireless network less secure than users and IT professionals have a right to expect. Therefore, you should expect the wireless hardware you buy to support it now.
Product categories
Sources: Wi-fi.org, Lifewire, HP
Are you looking to break into the exciting field of cybersecurity? Join our 5-day CompTIA Security+ Bootcamp Training and build your cybersecurity knowledge and skills.
Or
Become a certified ethical hacker! Our 5-day CEH Bootcamp is unlike other strictly theoretical training, you will be immersed in interactive sessions with hands-on labs after each topic. You can explore your newly gained knowledge right away in your classroom by pentesting, hacking and securing your own systems. Learn more






