CryptoLocker Ransomware Attack
CyptoLocker botnet is one of the oldest forms of cyber attacks which has been around for the past two decades. The CyptoLocker ransomware came into existence in 2013 when hackers used the original CryptoLocker botnet approach in ransomware.
CyptoLocker ransomware is the most destructive form of ransomware since it uses strong encryption algorithms. It is often impossible to decrypt (restore) the Crypto ransomware-infected computer and files without paying the ransom.
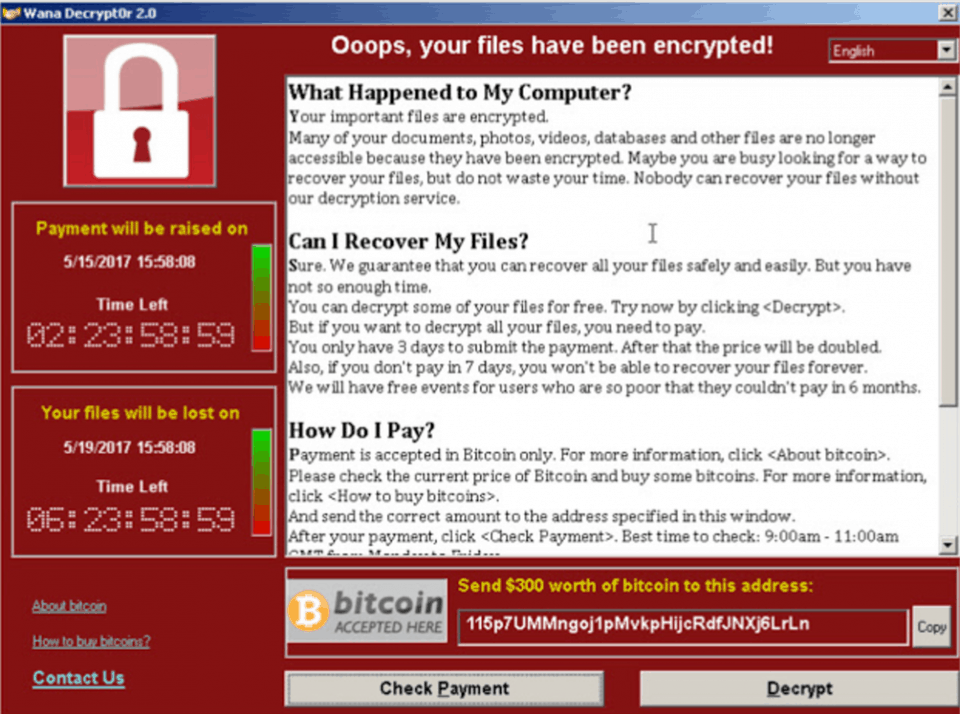
WannaCry Ransomware Attack
WannaCry is the most widely known ransomware variant across the globe. The WannaCry ransomware attack has affected nearly 125,000 organizations in over 150 countries. Some of the alternative names given to the WannaCry ransomware are WCry or WanaCrypt0r.
Cerber Ransomware Attack
Cerber ransomware attacks targeted cloud-based Office 365 users. Millions of Office 365 users have fallen prey to an elaborate phishing campaign carried out by the Cerber ransomware
CryptoWall Ransomware Attack
CryptoWall is an advanced form of CryptoLocker ransomware. It came into existence since early 2014 after the downfall of the original CryptoLocker variant. Today, there are multiple variants of CryptoWall in existence. It includes CryptoDefense, CryptoBit, CryptoWall 2.0, and CryptoWall 3.0.
Locky Ransomware Attack
Locky is another ransomware variant which is designed to lock the victim’s computer and prevent them from using it until a ransom is paid. It usually spread through a seemingly benign email message disguised as an invoice.
GoldenEye Ransomware Attack
GoldenEye is similar to the infamous Petya ransomware. It spreads through a massive social engineering campaign that targets human resources departments. When a user downloads a GoldenEye-infected file, it silently launches a macro which encrypts files on the victim’s computer.
Jigsaw Ransomware Attack
Jigsaw is one of the most destructive types of ransomware attacks, because it encrypts and progressively deletes the encrypted files until a ransom is paid. It starts deleting the files one after the other on an hourly basis until the 72-hour mark- when all the remaining files are deleted.
When a user opens the email attachment, the invoice gets deleted automatically, and the victim is directed to enable macros to read the document. When the victim enables macros, it begins encrypting multiple file types using AES encryption.
Apart from the list of ransomware mentioned above, Petya, NotPetya, TeslaCrypt, TorrentLocker, ZCryptor, etc., are some of the other ransomware variants that are well-known for their malicious activities.