How to prepare for CompTIA Network + Job? Questions Answers 1. What are the different layers of the OSI model, and can you explain each one? The OSI model has seven layers: Physical, Data Link, Network, Transport, Session, Presentation, and Application. Each layer is responsible for specific functions in network communication. 2. What is subnetting,… Read more »
Posts Tagged: Certification
CompTIA NET+ | Server Message Block Protocol (SMB)
Server Message Block Protocol (SMB) The Server Message Block (SMB) Protocol is a Microsoft Windows protocol that allows users to share files, printers, and serial ports across a network. SMBv2 is the most recent version released with Windows Vista and has undergone more revisions under Windows 7. The IBM-developed Server Message Block protocol is a… Read more »
CompTIA NET+ | Virtual Private Network (VPN)
What is VPN in Computer Network? VPN stands for Virtual Private Network. It allows you to connect your computer to a private network, creating an encrypted connection that masks your IP address to securely share data and surf the web, protecting your identity online. A virtual private network, or VPN, is an encrypted connection over the… Read more »
CompTIA NET+ | Single Mode vs. Multimode Fiber Optic Cables
Single Mode vs. Multimode Fiber Optic Cables Many decisions come into play when installing fiber optic cabling. By far, one of the most important questions is whether to install single mode or multimode. This decision has huge implications for your network’s distance, bandwidth, and budget, so it’s vital to understand the differences between these two… Read more »
CompTIA NET+ | Network Time Protocol (NTP)
Network Time Protocol (NTP) NTP is an internet protocol that’s used to synchronize the clocks on computer networks to within a few milliseconds of universal coordinated time (UTC). It enables devices to request and receive UTC from a server that, in turn, receives precise time from an atomic clock. What Is NTP? “A man with… Read more »
CompTIA NET+ | Distinguish between Connection-Oriented and Connectionless Service
Distinguish between Connection-Oriented and Connectionless Service Connection-Oriented Services In a connection-oriented service, each packet is related to a source/destination connection. These packets are routed along a similar path, known as a virtual circuit. Thus, it provides an end-to-end connection to the client for reliable data transfer. It delivers information in order without duplication or missing… Read more »
CompTIA NET+ | Simple Network Management Protocol (SNMP)
Simple Network Management Protocol (SNMP) SNMP stands for Simple Network Management Protocol. It is an Internet-standard protocol for handling devices on IP networks. Devices that typically provide SNMP include routers, switches, servers, workstations, printers, modem racks, and more. It is used mainly in the network management framework to monitor network-attached computers for conditions requiring regulatory attention…. Read more »
CompTIA NET+ | Dynamic Host Configuration Protocol (DHCP)
Dynamic Host Configuration Protocol (DHCP) Dynamic Host Configuration Protocol (DHCP) is a client/server protocol that automatically provides an Internet Protocol (IP) host with its IP address and other related configuration information such as the subnet mask and default gateway. In DHCP, port number 67 is used for the server and 68 is used for the… Read more »
CompTIA NET+ | Generic Routing Encapsulation (GRE)
CompTIA NET+ | Generic Routing Encapsulation (GRE) Generic Routing Encapsulation (GRE) is a routing protocol developed by Cisco Systems in 1994 that allows a wide range of network-layer protocols to be contained inside virtual point-to-point or point-to multipoint links over an Internet Protocol network. Protocol encapsulation, not GRE specifically, breaks the layering sequence, according to… Read more »
CompTIA A+ | Microsoft MTA O/S: Different Motherboard Form Factors
Follow @ASM_Educational What are the Different Motherboard Form Factors? Microsoft MTA O/S | CompTIA A+ Exam objectives 1.2: sizes. Introduction to Motherboards A motherboard (MB), also known as a Mainboard, system board or logic board, is the central or primary circuit board in a Personal Computer (PC). It is an extremely complex electronic… Read more »
CompTIA A+ | Microsoft MTA O/S: Backup and recovery
Follow @ASM_Educational Backup and recovery procedures protect your data against data loss and reconstruct the data, should loss occur. When searching for a backup solution, you’ll find that there are two main types of backups: “file-level backup” and “image-level backup.” File-Level Backup File-level backups are the most common type of backup. This method has been… Read more »
CompTIA A+ | Microsoft MTA O/S: Training (Display Adapters and Monitors)
Follow @ASM_Educational Source by Wikipedia Monitor Connectors: · If you are using a Monochrome / CGA/ EGA monitor, it is a digital monitor and will have a DB-9 Male connector that plugs into a digital adapter. · If you are using a VGA/ SVGA monitor, it will have a male DB-15 connector that plugs into… Read more »
CompTIA A+ | Microsoft MTA O/S: Training (Laptop Buses)
Follow @ASM_Educational Source by Wikipedia A bus is a set of signal pathways that allow information to travel between components inside or outside of a computer. Laptop Buses PCMCIA or PC Card Personal Computer memory card international association is a type of bus use for laptops. There are different types of cards and you primarily… Read more »
CompTIA A+ | Microsoft MTA O/S: Training (Other Types of Bus)
Follow @ASM_Educational Source by Wikipedia A bus is a set of signal pathways that allow information to travel between components inside or outside of a computer. Other Types of Bus USB USB or Universal Serial Bus is an external bus that most popular form of bus use today USB is hot swappable USB can daisy-chain… Read more »
CompTIA A+ | Microsoft MTA O/S: Types of Buses
Follow @ASM_EducationalSource by Wikipedia A bus is a set of signal pathways that allow information to travel between components inside or outside of a computer. Types of Bus External bus or Expansion bus allows the CPU to talk to the other devices in the computer and vice versa. It is called that because… Read more »
CompTIA A+/Network+ | Microsoft MTA O/S / Networking: Straight-through, Crossover, and Rollover Wiring
Follow @ASM_Educational ComputerCableStore When talking about cable pinouts we often get questions as to the difference in Straight-through, Crossover, and Rollover wiring of cables and the intended use for each type of cable. These terms are referring to the way the cables are wired (which pin on one end is connected to which pin… Read more »
CompTIA A+ | Microsoft MTA O/S: MOD Advanced Computer Troubleshooting II

Follow @ASM_Educational Source Quizlet What are three common problem areas with laptops? Displays Storage devices and RAM Power and input devices What tasks are associated with verifying work order information? Troubleshooting What are the three possible areas that a technician must check for printer errors? The device Cable connection The… Read more »
CompTIA A+ | Microsoft MTA O/S: MOD Advanced Computer Troubleshooting I
Follow @ASM_Educational Source Quizlet Most often, what is the reason for a need for advanced troubleshooting? It means that the probable cause is difficult to diagnose What are the six steps of troubleshooting? Identify the problem Establish a theory of probable cause Test the theory to determine the cause Establish a plan… Read more »
CompTIA A+ | Microsoft MTA O/S: Binary and Hexidecimal Conversion Tutorial
Follow @ASM_Educational Source Learning About Computers What are binary numbers? The binary number system is when only two numbers are used – 0 and 1. It is also called base 2. The computer number system is base 2. Our number system is referred to as decimal or base 10 because we use 10 digits… Read more »
CompTIA A+ | Microsoft MTA O/S: How To Install a Power Supply
Follow @ASM_Educational Source Learning About Computers To install a power supply is really quite easy. It fits in the top back of the case. First, orient the holes on the power supply to those on the case. Then, place the unit in the space provided and slide it in until the screw holes are aligned…. Read more »
CompTIA A+ | Microsoft MTA O/S: Where should fingers be placed on the keyboard?
Source Computer Hope As you can see in the picture below, your left-hand fingers should be placed over the A, S, D, and F keys and your right-hand fingers should be placed over the J, K, L, and ; keys.
CompTIA A+ | Microsoft MTA O/S: -Thermal printer

Source: Adopted From www.computerhope.com 1. A thermal impact printer or electrothermal printer is a printer that uses heated pins to “burn” images onto heat-sensitive paper.
CompTIA A+ | Microsoft MTA O/S: -Inkjet printer
Source: Adopted From www.computerhope.com The most popular printer for home computer users that prints by spraying streams of quick-drying ink on paper. The ink is stored in disposable ink cartridges, often a separate cartridge is used for each of the major colors.
CompTIA A+ | Microsoft MTA O/S: LED Printer
Source: Adopted From www.computerhope.com Similar to a laser printer, LED printers are non-impact but use a light-emitting diode instead of a laser in the printhead.
CompTIA A+ | Microsoft MTA O/S: Laser printer
Source: Adopted From www.computerhope.com First developed at Xerox PARC by Gary Starkweather and released in 1971, a laser printer is a printer that utilizes laser technology to print images on the paper.
CompTIA A+ | Microsoft MTA O/S: Dot matrix Printer
Source: Adopted From www.computerhope.com 1. The term Dot matrix refers to the process of using dots to form an image. In a dot matrix image, the image quality is determined by the number of dots per inch.
CompTIA A+ | Microsoft MTA O/S: AIO Printer
Source: Adopted From www.computerhope.com Alternatively referred to as a Multifunction printer(MFP), AIO is short for All-In-One. It is used to describe a hardware device such as an all-in-one printerthat is a printer, fax, and scanner all in one device.
CompTIA A+ | Microsoft MTA O/S: Printer
Source: Adopted From www.computerhope.com A printer is an external hardware output device responsible for taking electronic data stored on a computer or computing device and generating a hard copy of that data.
CompTIA A+ | Microsoft MTA O/S: Riser board

Source: Adopted From www.computerhope.com A riser board is a circuit board that gives a computer motherboard the option for additional expansion cards to be added to the computer.
CompTIA A+ | Microsoft MTA O/S: How to connect an external monitor to my laptop
Source: Adopted From www.computerhope.com Almost all laptops can connect to an external display and have the laptop display sent to that external display instead of, or in addition to, the laptop screen. Examples of an external display include a CRT monitor, flat panel display, projector, or TV.
CompTIA A+ | Microsoft MTA O/S: What can I upgrade in a laptop?
Source: Adopted From www.computerhope.com Unlike a desktop computer, laptops and other portable computers often do not offer many upgrade options. Below is a listing of common laptop upgrade questions and the answers to each of the questions regarding laptop and portable computer upgrades.
CompTIA A+ | Microsoft MTA O/S: How a virus works
Source Computer Hope The word “virus” is often used as a common term for all malicious programs, but technically a virus is a program or code that attaches itself to a legitimate, executable piece of software, and then reproduces itself when that program is run.
CompTIA A+ | Microsoft MTA O/S: What is Spyware?
Spyware can invade your privacy by recording, passing on and abusing your personal details – including credit card details – all of it behind your back.
CompTIA A+ | Microsoft MTA O/S: What is a computer worm?
An essential guide on computer worms and how they actually work A computer worm is similar to a computer virus, but unlike a virus it does not need to attach itself to an existing program.
CompTIA A+ | Microsoft MTA O/S: What is a rootkit?
Source: Adopted From www.bullguard.com All the information you need on rootkits and how to remove them
CompTIA A+ | Microsoft MTA O/S: How to Remove Malware
Source: Adopted From www.myturbopc.com “Malware” is short for “malicious software” – computer programs designed to infiltrate and damage computers without the users consent.
CompTIA A+ | Microsoft MTA O/S: How to find how much RAM is installed on a computer
Source: Adopted From www.computerhope.com Find how much RAM is installed and available in Windows 8 and 10
CompTIA A+ | Microsoft MTA O/S: Why is my online game so slow?
Source: Adopted From www.computerhope.com A game’s online performance can be attributed to many factors. Below is a listing of some of the different causes of why an online game may be slow or laggy.
CompTIA A+ | Microsoft MTA O/S: How Can I Fix My Slow Computer?
Source: Adopted From www.computerhope.com [bs_icon name=”glyphicon glyphicon-exclamation-sign”]Tip: This page only covers an overall slow computer and not a computer that has a slow boot up or slow Internet.
CompTIA A+ | Microsoft MTA O/S: Why is my Internet connection so slow?
Source: Adopted From www.computerhope.com A slow Internet connection can be caused by any number of reasons. Below is a short list of some of the more common reasons your Internet connection may be slow.
CompTIA A+ | Microsoft MTA O/S: My Windows computer boots up slow
Source: Adopted From www.computerhope.com A slow Microsoft Windows boot up can be caused by a number of different issues. The following document contains various suggestions and tips that can help improve the overall speed of your computer’s startup.
CompTIA A+ | Microsoft MTA O/S: Testing my computer motherboard and CPU for failures?
A bad computer motherboard or CPU can cause an assortment of different issues on your computer. Below are just a few of the possible issues you may encounter. It is important to remember that the issues below can also be caused by more than just a bad motherboard and CPU.
CompTIA A+ | Microsoft MTA O/S: Heat sink
A heat sink is an electronic device that incorporates either a fan or a peltier device to keep a hot component such as a processor cool.
CompTIA A+| Microsoft MTA O/S: Fan

A hardware device that keeps the overall computer or a computer device cool by circulating air to or from the computer or component. The picture is an example of a fan on a heat sink.
CompTIA A+ | Microsoft MTA O/S: Chipset

A chipset is a group of microchips that are designed to work with one or more related functions that were first introduced in 1986 when Chips and Technologies introduced the 82C206.
CompTIA A+ | Microsoft MTA O/S: What is the difference between BIOS and CMOS?

The BIOS and CMOS are often times thought to be the same thing, but they are not.
CompTIA A+ | Microsoft MTA O/S: Northbridge and Southbridge
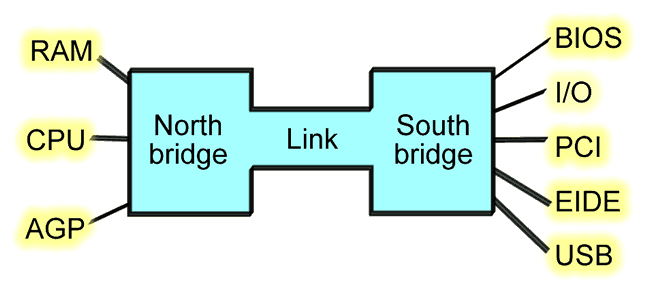
Southbridge The southbridge is an IC on the motherboard responsible for the hard drivecontroller, I/O controller and integrated hardware. Integrated hardware can include the sound card and video card if on the motherboard, USB, PCI, ISA, IDE, BIOS, andEthernet.
CompTIA A+ | Microsoft MTA O/S: Super I/O
Short for super input/output or Super I/O, SIO is anintegrated circuit on a computer motherboard that handles the slower and less prominent input/output devices shown below.
CompTIA A+ | Microsoft MTA O/S: Parallel port

Less commonly referred to as the Centronics interface or Centronics connectorafter the company that originally designed it, the port was later developed by Epson.
CompTIA A+ | Microsoft MTA O/S: Game control adapter
Originally known as the Analog-to-Digital port (A-to-D port), the as a game port, joystick port, or game control adapter is a 15-pin connector port first found onIBM computers in 1981.







