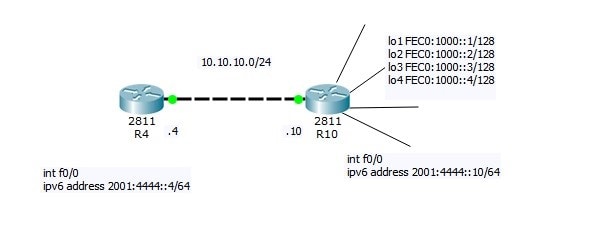
Follow @ASM_Educational Cisco CCNA EIGRP IPV6 Configuration Now I will do small Lab: R4=10.10.10.4 R10=10.10.10.10 connected via LAN link
Follow @ASM_Educational Cisco CCNA EIGRP IPV6 Configuration Now I will do small Lab: R4=10.10.10.4 R10=10.10.10.10 connected via LAN link
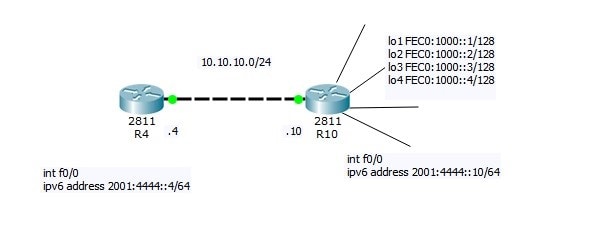
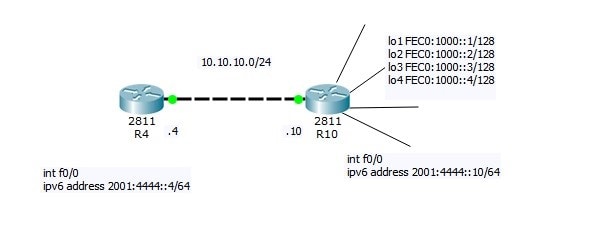
Follow @ASM_Educational Cisco CCNA OSPF IPV6 Configuration Now I will do small Lab: R4=10.10.10.4 R10=10.10.10.10 connected via LAN link
Follow @ASM_Educational Source Logical Operations Get our complete tutorial in PDF Related Links: Configuring IPv4 Configuring IPv6 Want more information on how to become Cisco CCNA Certified? Learn more! Join our Cisco CCNA facebook study group!
Follow @ASM_Educational Source Logical Operations Get our complete tutorial in PDF Configuring IPv6 Overview of IPv6 Implement IPv6 Addressing Implement IPv6 and IPv4 Transition from IPv4 to IPv6
Follow @ASM_Educational Source Logical Operations Get our complete tutorial in PDF Configuring IPv6 Overview of IPv6 Implement IPv6 Addressing Implement IPv6 and IPv4 Transition from IPv4 to IPv6
Follow @ASM_Educational Source Logical Operations Get our complete tutorial in PDF Configuring IPv4 Overview of the TCP/IP Protocol Suite Describe IPv4 Addressing Implement Subnetting and Supernetting Configure and Troubleshoot IPv4
Follow @ASM_Educational Description of OSI layers The recommendation X.200 describes seven layers, labeled 1 to 7. Layer 1 is the lowest layer in this model.
The nature of cyberattacks is constantly in flux, always evolving to keep pace with the times. Hacking of websites, theft of credit card information and other personal information has become an almost daily occurrence, along with illegal remittances via Internet banking. Recent years have witnessed the accelerating dissemination of new technologies such as IoT… Read more »
“Richard Clarke, a former counter-terrorism expert for the United Government, once said, “If you spend more on coffee than on IT security, you will be hacked. What’s more, you deserve to be hacked”. While the latter is a tad harsh (we wouldn’t wish a cyber attack on anyone!), the former is certainly true.” If you… Read more »

1. Your manager asks you to implement a system that can filter out unwanted content, such as viruses and unproductive Internet content. The best way to accomplish this would be through a system that implements a:
In this cram guide, we would like to give you some short tips on what to study for the Security+ exam to ensure a great score.