The nature of cyberattacks is constantly in flux, always evolving to keep pace with the times. Hacking of websites, theft of credit card information and other personal information has become an almost daily occurrence, along with illegal remittances via Internet banking. Recent years have witnessed the accelerating dissemination of new technologies such as IoT and the expanding utilization of information communication technology. Massive DDoS attacks have been launched using vulnerable IoT devices as springboards, while large-scale power outages have occurred due to attacks on critical infrastructure. Also whole factories, are connected to networks, there is an increased risk that factories and other manufacturing centers, as well as infrastructure, will become targets of cyber attacks. This makes security measures more important than ever before, and the best way to protect yourself and your company is to know about these different types of cyber attacks. Then you can use that information to take steps to make sure that your networks and devices are secure against any attacks. Below are some common terms for service attacks topic.
Man in the middle attack
What is man in the middle attack?
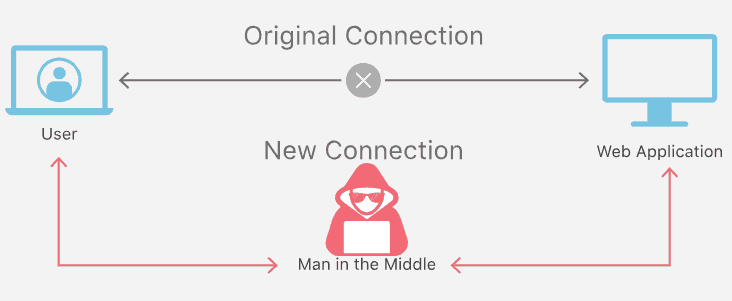
A man-in-the-middle attack (MITM) is an attack where the attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other. One example of a MITM is active eavesdropping, in which the attacker makes independent connections with the victims and relays messages between them to make them believe they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker. The attacker must be able to intercept all relevant messages passing between the two victims and inject new ones (Wikipedia, n.d.).
How does a man-in-the-middle attack work?
How does this play out? Let’s say you received an email that appeared to be from your bank, asking you to log in to your account to confirm your contact information. You click on a link in the email and are taken to what appears to be your bank’s website, where you log in and perform the requested task.
In such a scenario, the man in the middle (MITM) sent you the email, making it appear to be legitimate. (This attack also involves phishing, getting you to click on the email appearing to come from your bank.) He also created a website that looks just like your bank’s website, so you wouldn’t hesitate to enter your login credentials after clicking the link in the email. But when you do that, you’re not logging into your bank account, you’re handing over your credentials to the attacker.
Injection Attacks
What is Injection Attacks?
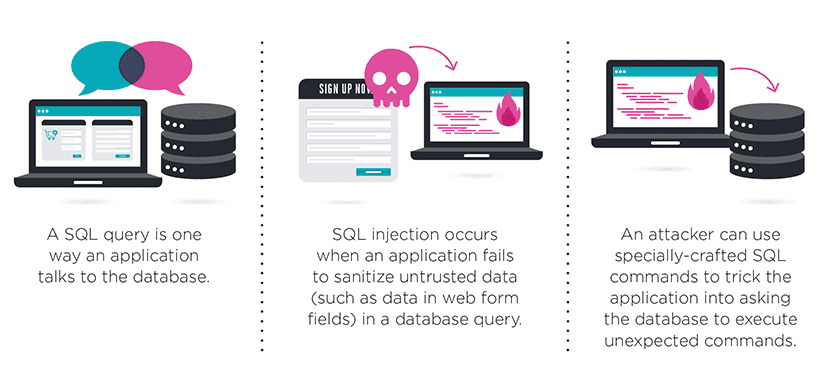
Injection is the exploitation of a computer bug that is caused by processing invalid data. Injection is used by an attacker to introduce (or “inject”) code into a vulnerable computer program and change the course of execution. The result of successful code injection can be disastrous, for example by allowing computer worms to propagate.
Code injection vulnerabilities (injection flaws) occur when an application sends untrusted data to an interpreter. Injection flaws are most often found in SQL, LDAP, XPath, or NoSQL queries; OS commands; XML parsers, SMTP headers, program arguments, etc. Injection flaws tend to be easier to discover when examining source code than via testing (Wikipedia, n.d.).
The most common injection attack.
Structured Query Language (SQL*) Injection is a code injection technique used to modify or retrieve data from SQL databases. By inserting specialized SQL statements into an entry field, an attacker is able to execute commands that allow for the retrieval of data from the database, the destruction of sensitive data, or other manipulative behaviors.
With the proper SQL command execution, the unauthorized user is able to spoof the identity of a more privileged user, make themselves or others database administrators, tamper with existing data, modify transactions and balances, and retrieve and/or destroy all server data.
In modern computing, SQL injection typically occurs over the Internet by sending malicious SQL queries to an API endpoint provided by a website or service (more on this later). In its most severe form, SQL injection can allow an attacker to gain root access to a machine, giving them complete control.
Privilege escalation
What is Privilege escalation?
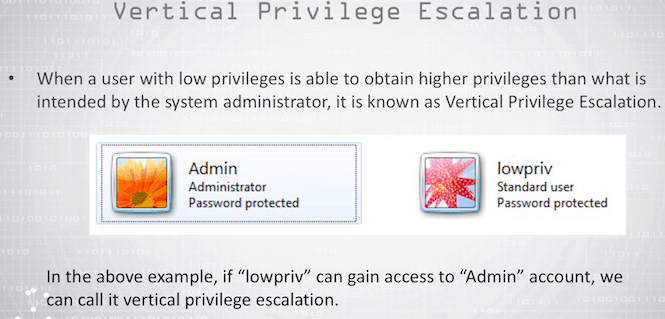
Privilege escalation is the act of exploiting a bug, design flaw or configuration oversight in an operating system or software application to gain elevated access to resources that are normally protected from an application or user. The result is that an application with more privileges than intended by the application developer or system administrator can perform unauthorized actions (wikipedia.org, n.d.).
Example of Privilege escalation attack.
Common examples of vertical privilege escalation attacks are lock screen bypasses on many of today’s popular smartphones. Android and iOS have both been affected by such vulnerabilities, which allow an unauthorized user to gain access to someone else’s contacts and apps just by performing a simple hack. Jailbreaking or Rooting — bypassing the manufacturer’s programming restrictions to take full control of a smartphone or other device is also an example of a privilege escalation attack.
ARP poisoning
What is ARP poisoning?
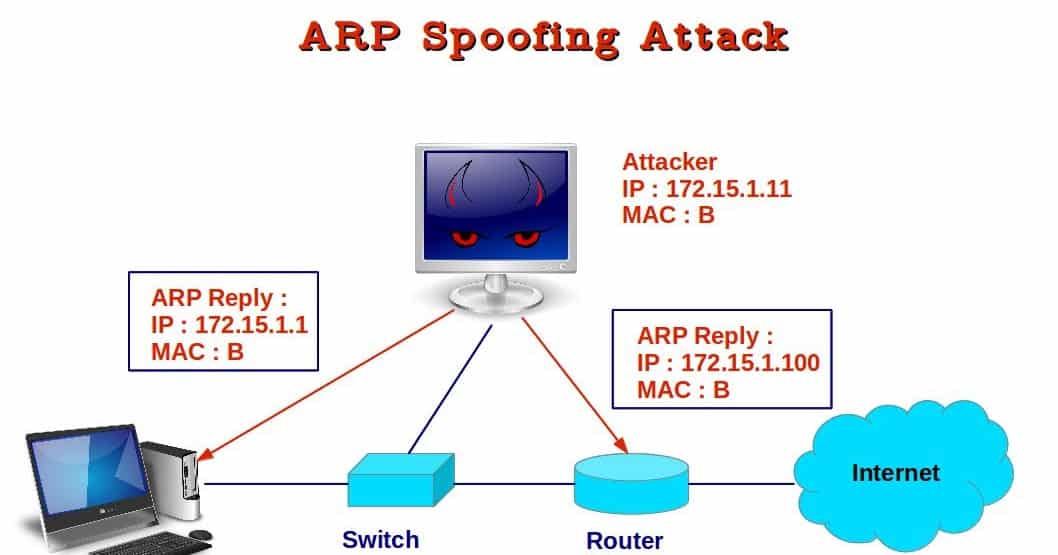
ARP poisoning or ARP spoofing is a type of attack in which a malicious actor sends falsified ARP (Address Resolution Protocol) messages over a local area network. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network. Once the attacker’s MAC address is connected to an authentic IP address, the attacker will begin receiving any data that is intended for that IP address. ARP spoofing can enable malicious parties to intercept, modify or even stop data in-transit. ARP spoofing attacks can only occur on local area networks that utilize the Address Resolution Protocol (veracode, n.d.).
Amplification
What is An Amplification Attack?
An Amplification Attack is any attack where an attacker is able to use an amplification factor to multiply its power. Amplification attacks are “asymmetric”, meaning that a relatively small number or low level of resources is required by an attacker to cause a significantly greater number or higher level of target resources to malfunction or fail. Examples of amplification attacks include Smurf Attacks (ICMP amplification), Fraggle Attacks (UDP amplification), and DNS Amplification (radware.com, n.d.).
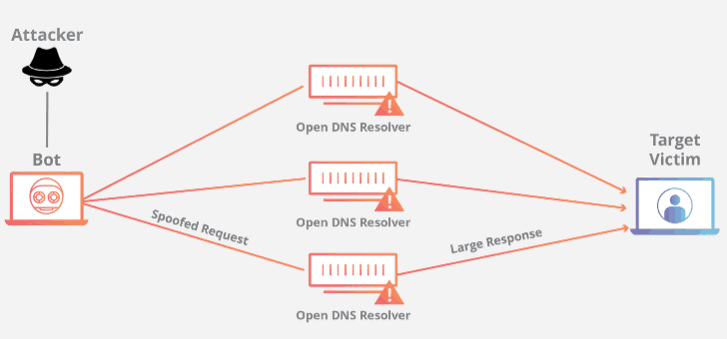
DNS amplification attack
This DDoS attack is a reflection-based volumetric distributed denial-of-service (DDoS) attack in which an attacker leverages the functionality of open DNS resolvers in order to overwhelm a target server or network with an amplified amount of traffic, rendering the server and its surrounding infrastructure inaccessible.
What is the biggest DDOS attack ever recorded?
March 2018, the developer platform GitHub was hit by the most powerful distributed denial of service attack recorded to date with about 1.35 terabits per second of traffic going in to the GitHub servers. Unlike the formal botnet attacks used in large DDoS efforts, like against Dyn and the French telecom OVH, memcached DDoS attacks don’t require a malware-driven botnet. Attackers simply spoof the IP address of their victim and send small queries to multiple memcached servers—about 10 per second per server—that are designed to elicit a much larger response. Known as an amplification attack, The memcached systems then return 50 times the data of the requests back to the victim.
Man In the Browser
What is Man in the Browser Attack (MITB)?
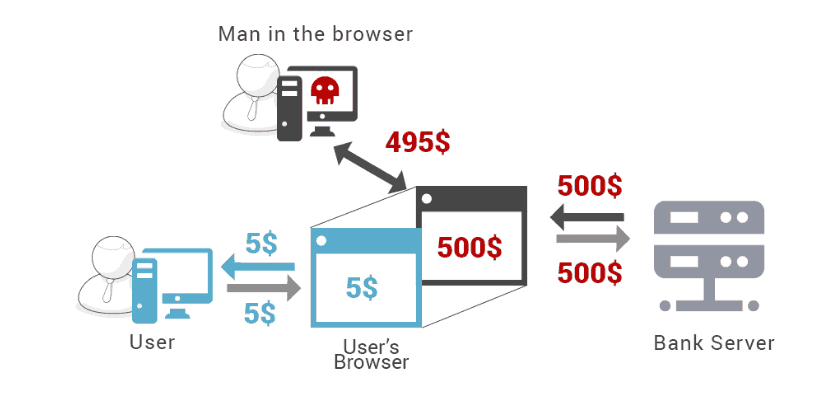
The man-in-the-browser (MITB) attack utilizes a Trojan Horse in a pre-infected device/system to infect the internet browser, and sniff, capture and modify information as it travels between the user interface of the infected browser and the internet (wikipedia.org, n.d.).
MITB malware is a Trojan that infects endpoints through malicious email attachments, links, or even when a user visits an infected website. Cyber criminals target victims through social engineering – phishing and targeted spearphishing attacks to attempt infection.
What does MITB do?
Man-in-the-Browser (MITB) malware can view and steal information as a user types into the browser. It can also directly modify the elements in the user’s browser and also inject content such as new fields without the user knowing about it. This in effect changes the functionality of the webpage. As an example, the MITB malware can inject a field for entry of date of birth, social security number or passport number in the login form. As the original URL and SSL protections are retained, the victim will not suspect the webpage.
The MITB malware can also fool the webpage server by injecting its own JavaScript using the stolen credentials. If the webpage belongs to a banking institution then it could be fooled into allowing it to perform online financial transfers or payments. The bank would think that the legitimate user had initiated the transaction. Some MITB malware is so advanced that even when the user logs into the next time, the fund transfer or debit of money is not displayed.
Zero day
What is zero day?
A zero day exploit is a cyber attack that occurs on the same day a weakness is discovered in software. At that point, it’s exploited before a fix becomes available from its creator.
Initially when a user discovers that there is a security risk in a program, they can report it to the software company, which will then develop a security patch to fix the flaw. This same user may also take to the Internet and warn others about the flaw. Usually the program creators are quick to create a fix that improves program protection, however, sometimes hackers hear about the flaw first and are quick to exploit it. When this happens, there is little protection against an attack because the software flaw is so new (kaspersky, n.d.).
Recent Zero-Day Exploits
As of March 2019, Google revealed that it sent out a fix for Chrome Browser for a zero-day that was under active attacks.
Google described the security flaw as a memory management error in Google Chrome’s FileReader –a web API included in all major browsers that lets web apps read the contents of files stored on the user’s computer.
More specifically, the bug is a use-after-free vulnerability, a type of memory error that happens when an app tries to access memory after it has been freed/deleted from Chrome’s allocated memory. An incorrect handling of this type of memory access operation can lead to the execution of malicious code.
According to Chaouki Bekrar, CEO of exploit vendor Zerodium, the CVE-2019-5786 vulnerability allegedly allows malicious code to escape Chrome’s security sandbox and run commands on the underlying OS (Cimpanu, 2019).
Zero-day attacks are cyber attacks against software flaws that are unknown and have no patch or fix.
It’s extremely difficult to detect zero-day attacks, especially with traditional cyber defenses. Traditional security measures focus on malware signatures and URL reputation. However, with zero-day attacks, this information is, by definition, unknown. Cyber attackers are extraordinarily skilled, and their malware can go undetected on systems for months, and even years, giving them plenty of time to cause irreparable harm.
Be an Ethical Hacker! Check out our CompTIA Security+ certification program. Click here
References
Cimpanu, C. (2019, 03 06). Google reveals Chrome zero-day under active attacks. Retrieved from zdnet.com: https://www.zdnet.com/article/google-reveals-chrome-zero-day-under-active-attacks/
kaspersky. (n.d.). What is Zero Day Exploit? Retrieved from usa.kaspersky.com: https://usa.kaspersky.com/resource-center/definitions/zero-day-exploit
radware.com. (n.d.). Amplification Attack. Retrieved from security.radware.com: https://security.radware.com/ddos-knowledge-center/ddospedia/amplification-attack/
veracode. (n.d.). ARP SPOOFING. Retrieved from www.veracode.com: https://www.veracode.com/security/arp-spoofing
Wikipedia. (n.d.). Retrieved from Wikipedia.com: https://en.wikipedia.org/wiki/Man-in-the-middle_attack
Wikipedia. (n.d.). Code Injection. Retrieved from wikipedia.org: https://en.wikipedia.org/wiki/Code_injection
wikipedia.org. (n.d.). Man-in-the-browser. Retrieved from wikipedia.org: https://en.wikipedia.org/wiki/Man-in-the-browser
wikipedia.org. (n.d.). Privilege escalation. Retrieved from wikipedia.org: https://en.wikipedia.org/wiki/Privilege_escalation







