Before you can delete a VPC, you must terminate any instances that are running in the VPC.
Monthly Archives:: May 2016
Amazon AWS-Step 4: Assign an Elastic IP Address to Your Instance
In the previous step, you launched your instance into a public subnet — a subnet that has a route to an Internet gateway. However, the instance in your subnet also needs a public IP address to be able to communicate with the Internet.
Amazon AWS-Step 3: Launch an Instance into Your VPC
When you launch an EC2 instance into a VPC, you must specify the subnet in which to launch the instance. In this case, you’ll launch an instance into the public subnet of the VPC you created.
Amazon AWS-Step 2: Create a Security Group
A security group acts as a virtual firewall to control the traffic for its associated instances. To use a security group, you add the inbound rules to control incoming traffic to the instance, and outbound rules to control the outgoing traffic from your instance.
Amazon AWS-Step 1: Create the VPC
In this step, you’ll use the Amazon VPC wizard in the Amazon VPC console to create a VPC. The wizard performs the following steps for you:
Amazon AWS-Getting Started with Amazon VPC
In this exercise, you’ll create a VPC and subnet, and launch a public-facing instance into your subnet.
Getting Started with Amazon Simple Storage Service
Amazon Simple Storage Service (Amazon S3) is storage for the Internet. You can use Amazon S3 to store and retrieve any amount of data at any time, from anywhere on the web. You can accomplish these tasks using the AWS Management Console, which is a simple and intuitive web interface. This guide introduces you to… Read more »
Introduction to Amazon S3
This introduction to Amazon Simple Storage Service is intended to give you a detailed summary of this web service. After reading this section, you should have a good idea of what it offers and how it can fit in with your business. Topics Overview of Amazon S3 and This Guide Advantages to Amazon S3 Amazon… Read more »
Working with Amazon S3 Buckets
Amazon S3 is cloud storage for the Internet. To upload your data (photos, videos, documents etc.), you first create a bucket in one of the AWS regions. You can then upload any number of objects to the bucket. In terms of implementation, buckets and objects are resources, and Amazon S3 provides APIs for you to… Read more »
Working with Amazon S3 Objects
Amazon S3 is a simple key, value store designed to store as many objects as you want. You store these objects in one or more buckets. An object consists of the following: Key – The name that you assign to an object. You use the object key to retrieve the object. For more information, see… Read more »
Managing Access Permissions to Your Amazon S3 Resources
By default, all Amazon S3 resources—buckets, objects, and related subresources (for example, lifecycleconfiguration and website configuration)—are private: only the resource owner, an AWS account that created it, can access the resource. The resource owner can optionally grant access permissions to others by writing an access policy. Amazon S3 offers access policy options broadly categorized as resource-based… Read more »
Amazon S3
Amazon S3 Amazon Simple Storage Service (Amazon S3), provides developers and IT teams with secure, durable, highly-scalable cloud storage. Amazon S3 is easy to use object storage, with a simple web service interface to store and retrieve any amount of data from anywhere on the web. With Amazon S3, you pay only for the storage… Read more »
Amazon AWS-What is Amazon VPC?
Source By: <docs.aws.amazon.com> Amazon Virtual Private Cloud (Amazon VPC) enables you to launch Amazon Web Services (AWS) resources into a virtual network that you’ve defined.
Setting Up with Amazon EC2
If you’ve already signed up for Amazon Web Services (AWS), you can start using Amazon EC2 immediately. You can open the Amazon EC2 console, click Launch Instance, and follow the steps in the launch wizard to launch your first instance.
What Is Amazon EC2?
Amazon Elastic Compute Cloud (Amazon EC2) provides scalable computing capacity in the Amazon Web Services (AWS) cloud. Using Amazon EC2 eliminates your need to invest in hardware up front, so you can develop and deploy applications faster.
Cisco CCNA OSI Model
Follow @ASM_Educational Description of OSI layers The recommendation X.200 describes seven layers, labeled 1 to 7. Layer 1 is the lowest layer in this model.
Cisco CCNA – Call Manager Express Part 2
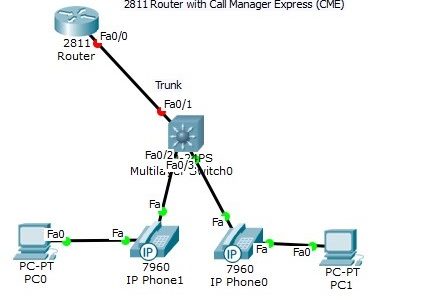
Follow @ASM_Educational The Trunk port between the router and switch had to be manually configured using sub-interfaces. Note, however, that the DATA vlan traffic and the phone VOICE vlan traffic for each host is carried over the same link (multiple vlan traffic over the same port).
Cisco CCNA – Call Manager Express Part 1
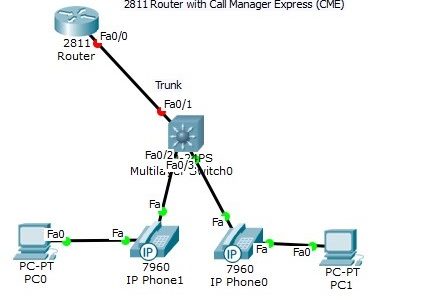
Follow @ASM_Educational Build the following topology in packet tracer. After testing our configuration, we will deploy on devices.
Cisco CCNA How to configure Multi-Layer Switch
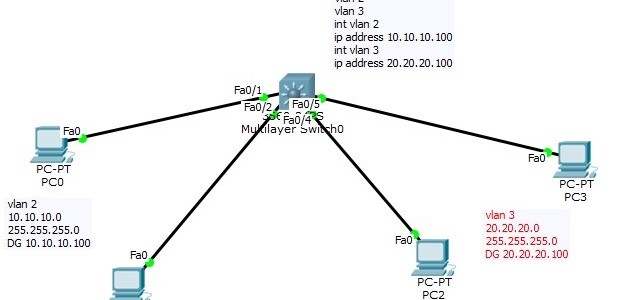
Follow @ASM_Educational Cisco CCNA- How to Configure Multi-Layer Switch Layer 3 Switch Now that we have seen how a “router on a stick” works, we can introduce the Layer 3 switch. In the “router on a stick” topology, what if we could bring the router inside the switch?
CompTIA Linux+ Configuration
Configuring your Xwindows No matter what desktop environment you chose, it is most likely that it will use the Xwindows architecture.
CompTIA Linux+ Installation
Media Linux installation can be done using a variety of different media. Each installation method has different pros and cons depending on the environment you have. Here are some examples:
CompTIA Linux+ Planning the Implemenation
Linux Uses Linux is a pretty flexible operating system. Although it has got a lot of credibility over the years as a stable server platform, it is also an excellent desktop platform. Databases, mail servers as well as many appliances can be installed.
CompTIA Linux+ What is Linux?
Linux is a 32 bit open source operating system. It is based on the very popular Unix operating system and it’s code is freely available (thus explaining the “open source” label as opposed to closed source where the code is not available freely).
What Is AWS Amazon S3?
Amazon Simple Storage Service is storage for the Internet. It is designed to make web-scale computing easier for developers.
CompTIA A+ | Microsoft MTA O/S: Heat sink
A heat sink is an electronic device that incorporates either a fan or a peltier device to keep a hot component such as a processor cool.
CompTIA A+| Microsoft MTA O/S: Fan

A hardware device that keeps the overall computer or a computer device cool by circulating air to or from the computer or component. The picture is an example of a fan on a heat sink.
CompTIA A+ | Microsoft MTA O/S: Chipset

A chipset is a group of microchips that are designed to work with one or more related functions that were first introduced in 1986 when Chips and Technologies introduced the 82C206.
CompTIA A+ | Microsoft MTA O/S: What is the difference between BIOS and CMOS?

The BIOS and CMOS are often times thought to be the same thing, but they are not.
CompTIA A+ | Microsoft MTA O/S: Northbridge and Southbridge
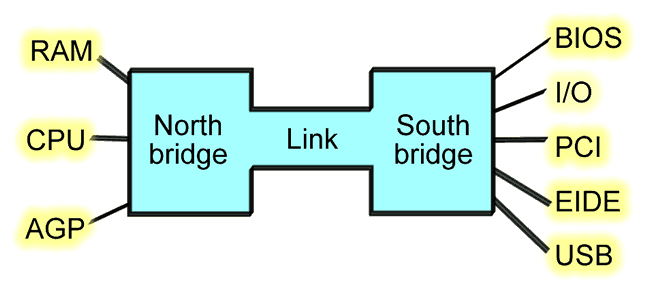
Southbridge The southbridge is an IC on the motherboard responsible for the hard drivecontroller, I/O controller and integrated hardware. Integrated hardware can include the sound card and video card if on the motherboard, USB, PCI, ISA, IDE, BIOS, andEthernet.
CompTIA A+ | Microsoft MTA O/S: Super I/O
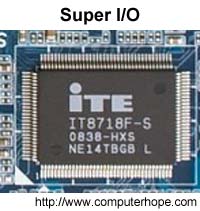
Short for super input/output or Super I/O, SIO is anintegrated circuit on a computer motherboard that handles the slower and less prominent input/output devices shown below.
CompTIA A+ | Microsoft MTA O/S: Parallel port

Less commonly referred to as the Centronics interface or Centronics connectorafter the company that originally designed it, the port was later developed by Epson.
CompTIA A+ | Microsoft MTA O/S: Game control adapter
Originally known as the Analog-to-Digital port (A-to-D port), the as a game port, joystick port, or game control adapter is a 15-pin connector port first found onIBM computers in 1981.
CompTIA A+ | Microsoft MTA O/S: How to replace the CMOS Battery

If your computer is losing its time or date settings, or you are receiving a messageCMOS Read Error, CMOS Checksum Error, or CMOS Battery Failure, the CMOS battery needs to be replaced. To do this, follow the steps below.
CompTIA A+ | Microsoft MTA O/S: What is CMOS Battery?

Alternatively referred to as a Real-Time Clock (RTC), Non-Volatile RAM (NVRAM) or CMOS RAM, CMOS is short for Complementary Metal-Oxide Semiconductor.
CompTIA A+ | Microsoft MTA O/S: How do I install an expansion card?
There are many types of expansion cards that can be installed in a computer, including sound, video, modem, network, interface card, and a number of others. In many cases, these expansion cards will fit in a slot in the computer called a PCI slot.
CISSP Security & Risk Management-Results from the BIA
Result contains: Identified critical functions and required resources
CISSP Security & Risk Management-Business Impact Analysis (BIA)
Identify organization’s critical business functions
CISSP Security & Risk Management-Disaster Recovery (DR)
Review the BIA BIA contains the prioritized list of critical business functions Should be reviewed for compatibility with the BC plan
CISSP Security & Risk Management- Business Continuity (BC) & Disaster Recovery (DR) Requirements
Project Initiation and Management Develop and Document Project Scope and Plan
CISSP Security & Risk Management- Global Legal and Regulatory Issues
Computer/Cyber Crime CryptoLocker Ransomware – Spreads via email and propagates rapidly. Encrypts various file types and then a pop-up window appears to inform user about the actions performed on computer and, therefore demand a monetary payment for files to be decrypted.
CISSP Security & Risk Management- Computer Crimes
Computer as incidental to other crimes Involves crimes where computers are not really necessary for such crimes to be committed. Instead computers facilitate these crimes and make them difficult to detect. Examples of crimes in this category may include money laundering and unlawful activities on bulletin board systems.
CompTIA Network+ | Microsoft MTA Networking: Common Security Threats
Source mc mcse Certification Resources DoS (Denial of Service) – A DoS attack is a common type of attack in which false requests to a server overload it to the point that it is unable to handle valid requests, cause it to reset, or shut it down completely.
CompTIA Network+ | Microsoft MTA Networking: Issues That Affect Device Security
Source mc mcse Certification Resources Physical Security – physical security is just as it sounds, locks on the doors, cameras everywhere, and so forth.
CompTIA Network+ | Microsoft MTA Networking: Methods of User Authentication
User authentication is the verification of an active human-to-machine transfer of credentials required for confirmation of a user’s authenticity; the term contrasts with machine authentication, which involves automated processes that do not require user input. Source mc mcse Certification Resources PKI (Public Key Infrastructure) – A public key infrastructure (PKI) is the combination of software,… Read more »
CompTIA Network+ | Microsoft MTA Networking: Network Access Security
Source mc mcse Certification Resources ACL (Access Control List) – An ACL is a table in an operating system or network device (such as a router) that denies or allows access to resources.
CompTIA Network+ | Microsoft MTA Networking: Firewalls
Source mc mcse Certification Resources Application Layer vs. Network Layer – An application layer firewall works at the application layer of a protocol stack.







