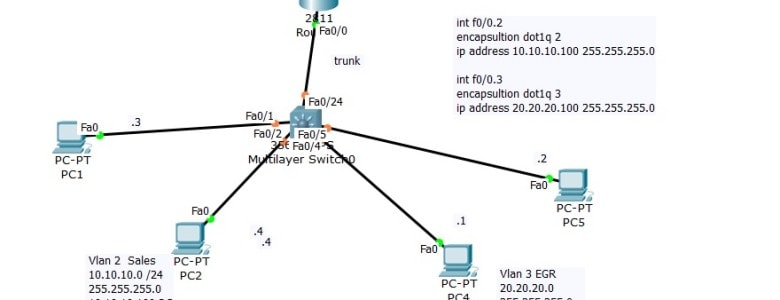
Follow @ASM_Educational Using DHCP Server with Inter-Vlan Routing (Router on stick) On Last Video we talked about the router on stick that is we made sure that client from Network 10.10.10.0 can communicate with Network 20.20.20.0
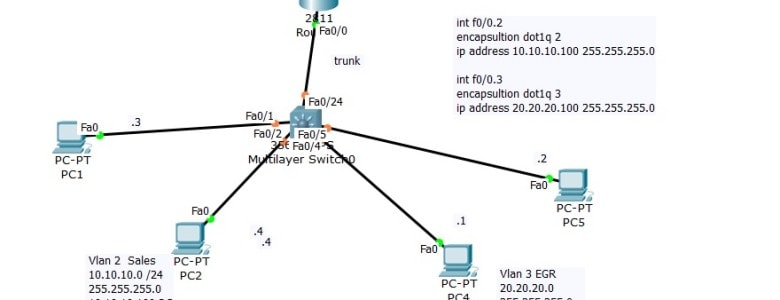
Follow @ASM_Educational Using DHCP Server with Inter-Vlan Routing (Router on stick) On Last Video we talked about the router on stick that is we made sure that client from Network 10.10.10.0 can communicate with Network 20.20.20.0
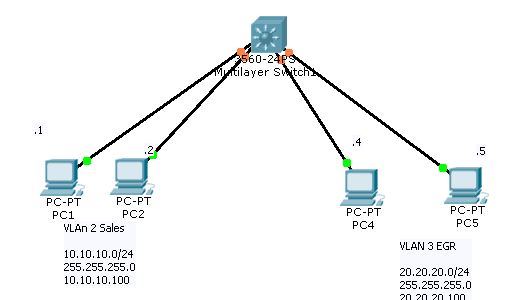
Follow @ASM_Educational Setting up VLAN’s On a new switch, all the ports are in VLAN 1 by default. We just plug in the Ethernet cables and the devices can communicate. Furthermore, all the ports are in the up/up (administratively up) mode.
Alternatively referred to as a bus slot or expansion port, an expansion slot is connection or port located inside a computer on the motherboard or riser board that allows a computer hardware expansion card to be connected.
Power Supplies Okay, now that we’ve tested our AC outlet and put some protective power devices into play, let’s go ahead and talk power supplies.
You may not typically handle the insides of your computers, but if your business requires knowledge of Central Processing Units (CPU), then you’ll also need to learn about CPU sockets
Computer port In computer hardware, a port serves as an interface between the computer and other computers or peripheral devices.
What does a hard drive do? Storage is the hard drive’s responsibility. Everything you keep on your computer is on a hard drive.
What Is Memory, or RAM? System memory, frequently called main memory or RAM (Random Access Memory), is a type of computer memory that can be accessed randomly.
Oversight Committee Representation
Organizational or corporate governance has existed since time immemorial to ensure the efficient running via control structures.
Wireless Communications WAP (Wireless Applications Protocol) –Developed for wireless (PDA’s, mobile phones, pagers, etc. devices to communicate)
Tunneling is a method of transferring data from one network to another by encapsulating the packets in an additional header. The additional header provides routing information so that the encapsulating payload traverse the intermediate networks.
IPSec IPSec is an architecture or framework for security services for IP networks. It works at the Network Layer of the OSI Model. It is actually a standard for secure data transmission. It provides mechanisms for authentication and encryption. Defined by RFC 4301 and carries a set of functions, it is mandatory in IPv6. IPSec… Read more »
Open Systems Interconnect (OSI) Model
WANS and Their Components Wide area networks (WANs) are considerably different than LANs. Organizations usually own their own LANs, but WAN services are typically leased; it’s not feasible to have your network guy run a cable from New York to Dallas.
Source mc mcse Certification Resources Cable Testers – Cable testers are electronic devices used to test a cable’s integrity by checking for opens and shorts which can cause connectivity problems.
Source mc mcse Certification Resources Crosstalk Symptoms: Slow network performance and/or an excess of dropped or unintelligible packets. In telephony applications, users hear pieces of voice or conversations from a separate line.
Source mc mcse Certification Resources Gather Information on the Problem In a contact center network, problems are typically discovered and reported by one of the following types of users:
Source mc mcse Certification Resources Bandwidth – is the average number of bits that can be transmitted from the source to a destination over the network in one second.

Follow @ASM_Educational Cisco CCNA-Router on Stick Inter VLAN Communication (Router on Stick) Earlier we built and tested the following topology:
The Types of Wireless Attacks Part 2 CompTIA Security+ Objective 1.2 WPS Attacks Wi-Fi Protected Setup (WPS) allows users to configure a wireless network without typing in the passphrase. Instead, users can configure devices by pressing buttons or by entering a short personal identification number (PIN). For example, a user can configure a new wireless… Read more »
The Types of Wireless Attacks Part 1 CompTIA Security+ Objective 1.2 Replay Attacks A replay attack occurs when an attacker copies a stream of messages between two parties and replays the stream to one or more of the parties. Unless mitigated, the computers subject to the attack process the stream as legitimate messages, resulting in a range… Read more »
CompTIA and Immersive Labs are challenging cybersecurity professionals in the United States and United Kingdom to test their penetration testing skills this month. The two organizations launched the pen test challenge on the opening day of RSA® Conference 2019. “Penetration testing, if done right, is a proven and valuable activity that all organizations should engage… Read more »
The nature of cyberattacks is constantly in flux, always evolving to keep pace with the times. Hacking of websites, theft of credit card information and other personal information has become an almost daily occurrence, along with illegal remittances via Internet banking. Recent years have witnessed the accelerating dissemination of new technologies such as IoT… Read more »
“Richard Clarke, a former counter-terrorism expert for the United Government, once said, “If you spend more on coffee than on IT security, you will be hacked. What’s more, you deserve to be hacked”. While the latter is a tad harsh (we wouldn’t wish a cyber attack on anyone!), the former is certainly true.” If you… Read more »

1. Your manager asks you to implement a system that can filter out unwanted content, such as viruses and unproductive Internet content. The best way to accomplish this would be through a system that implements a:
In this cram guide, we would like to give you some short tips on what to study for the Security+ exam to ensure a great score.
One of the most essential portions of information security is the design and topology of secure networks. What exactly do we mean by “topology?” Usually, a geographic diagram of a network comes to mind.
Definition – What does Malicious Software (Malware) mean? Malicious software, commonly known as malware, is any software that brings harm to a computer system. Malware can be in the form of worms, viruses, trojans, spyware, adware and rootkits, etc., which steal protected data, delete documents or add software not approved by a user.