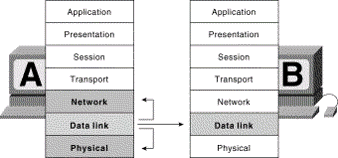
Open Systems Interconnect (OSI) Model
- Developed in the 1980s by the ISO
- Benefits:
- Interoperability
- Modularity
- Defined Interfaces/ Vendor & engineering specialization
Encapsulation: A process whereby all layers in the stack store data in a format required by the next layer.
–The seven Layers of the OSI Model Application Layer
| OSI MODEL | TCP/IP Model | |
| 7 | Application | Application |
| 6 | Presentation | |
| 5 | Session | |
| 4 | Transport | Transport |
| 3 | Network | Internet |
| 2 | Data Link | NetworkAccess |
| 1 | Physical |
TCP (Transmission Control Protocol)
–Often combined with IP and referred to as a suite of protocols; i.e. it includes a assortment of protocols.
- TCP is a connection-oriented protocol.
- It is a Layer 4 protocol
- TCP provides a full-duplex, reliable communication mechanism
- Requires much system resources (overhead)
- It sits on Layer 4 with UDP that is a connectionless protocol
IP (Internet Protocol, a.k.a. IPv4)
–Often bundled with TCP as a suite of protocols.
- IP is a connectionless protocol.
- Does not burden system resources
- It is a Layer 3 protocol
- IP Addressing
- Class A 0 – 127
- Class B 128 – 191
- Class C 192 – 223
- Class D 224 – 239
- Class E 240 – 255
IPv6 (Internet Protocol version 6; RFC 2460)
- Known as IP next gen
- Has IPSec integrated into its protocol stack and provides end-to-end secure transmission and authentication
- Has larger address space
- Has more flexibility and routing capabilities
- Allows for Quality of Service (QoS) priority values to be assigned to time-sensitive transmissions
- Set to overcome many of the limitations inherent in IPv4
Types of Transmission
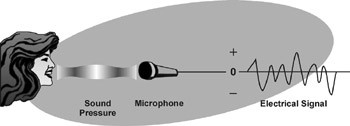
Analog – An analog signal can vary continuously between a maximum and minimum value and it can assume an infinite number of values between the two extremes.
- Analog information can be represented by a continuous and smoothly varying amplitude or frequency over a certain range such as voice or music.
- Frequency – is the number of complete cycles or wavelengths that the wave has in a given unit of time (second). The standard measurement for this is number of cycles per second, also known as Hertz (the scientist, not the car company), abbreviated Hz.
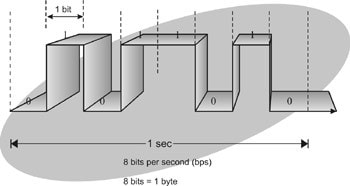
Digital – Signals represent binary digits as electrical pulses.
- Digital signals have a limited number of discrete states, usually two, that transfer signal levels at predetermined time intervals. The two levels of most digital signals are on (logic 1) and off (logic 0).
Asynchronous communications
–No clocking mechanism required
Synchronous communication
–Clocking mechanism required
Broadband
–Divides channel into many individual independent channels allowing more data to be transmitted in a given amount of time (analogy: much as more lanes on a highway allow more cars to travel along it at the same time)
Baseband
–A telecommunication system in which data is carried in digital form on a single unmultiplexed signal channel on the transmission medium as used in Ethernet.
–Uses the entire channel for transmission
Unicast
–When a packet is sent from one source to device to a one destination device.
Multicast
–When a packet is sent from one source device to several specific devices.
Broadcast
–When a packet is sent from one source to device to all devices within a network segment.
Circuit vs. Packet Switching
Circuit switching
- Connection-oriented virtual lines
- Traffic travels in a predictable and constant manner
- Fixed delays
- Usually carries voice-oriented data
Packet switching
- Packets can use many different dynamic paths to get to the same destination
- Traffic usually bursty in nature
- Variable delays
- Usually carries data-oriented data.
Routing Protocols
- Routing Information Protocol (RIP)
- Open Shortest Path First (OSPF)
- Interior Gateway Routing Protocol (IGRP)
Network Devices
- Repeaters
- Bridges
- Routers
- Switches
- Gateways
- PBXs
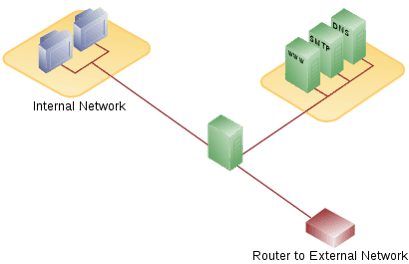
Firewalls
Block hostile traffic and allow authorized traffic to protect a network from an untrusted network.
Packet Filtering
–Packet filtering firewalls operate at the network layer of the OSI Model
–Packet filtering takes place using an Access Control List (ACL)
–The ACL provides information as to what packets can be accepted and what packets to be denied access
–This type of firewall compares the packet header with a set of rules in the ACL
Proxy Firewalls
–Inspects packets’ payload
–Offers better security than the first generation firewall
–Considered a second generation firewall
There are 3 types of Proxy Firewalls
–Application-level proxy
- Operates at the Application Layer of the OSI Model and makes access decisions based on the packet content – the payload.
- Because the packet is examined by the proxy at Layer 7 the firewall needs to completely understand all the protocols associated with packets.
- This firewall provides more granular control because it understands all the intricacies associated with a protocol and a service.
–Circuit-level proxy
- Operates at the Session Layer of the OSI Model and makes access decisions based on address, port and protocol type, and not on the packet content.
- This firewall creates a circuit between the client computer and the server.
- This firewall can work with a variety of protocols but does not offer as much granular control as the Application-level proxy firewall.
–Kernel proxy
- Operates at the Application Layer and considered as 5th Generation firewalls.
- When a packet arrives at a kernel proxy firewall, a new virtual stack is created that contains only the protocol proxies needed to examine the specific packet.
- The packet is investigated at every layer of the stack, which involves evaluating the data link header along with the network header, transport header, session layer information, and application layer data.
- These firewalls work faster than all the application-level firewalls because all evaluation takes place at the kernel and not at the higher layers of the operating system.
Stateful Inspection
–Usually Operates at the network layer of the OSI Model
–It investigates packet header, payload, and trailer
–Maintains a state table. This table contains information related to packets in previous connections and includes the source and destination IPs, source and destination ports, and acknowledgement bits
–The advantage of this firewall is added security because it keeps track of all packets until their connection are closed
–Also tracks connectionless protocols such as UDP and ICMP
–Known as a third generation firewall
- Honeypot – Decoy system that is usually deployed in a DMZ to lure attackers to instead of real production systems.
- Honeynet – A network of honeypots.
- Network Segregation & Isolation – For security and smooth network management.
DMZ – A section of network that is made available for public access.
VPN – Virtual Private Network
Provides:
- Privacy – prevents anyone in the middle of the Internet (man in the middle) from intercepting packets.
- Authentication – verifies that the sender of the VPN packet is a legitimate device and not one being used by an attacker.
- Data integrity – verifies that the packet was not changed as it traveled through the Internet.
- Anti-replay – prevents a man in the middle from copying packets sent by a legitimate user and then resends the packets as if he was a legitimate user.
To accomplish the above goals (privacy, authentication, data integrity, and anti-replay), two devices near the edge of the Internet create a VPN, sometimes called a VPN tunnel. These devices add headers to the original packet, including fields that allow the VPN devices to perform all the functions. The VPN devices also encrypt the original IP packet.
Site-to-Site : When a VPN connects two site of a company, in particular. Also sometimes called Gateway-to-Gateway.
Host-to-Site: When a VPN connects a user/device from a remote location (home/hotel) to a company. Also sometimes called Host-to-Gateway.
VPN – Implementation
SSL VPN – a browser is needed for connectivity. Usually implemented for users to access only web-based applications. It is easier to deploy on workstations than IPSec VPN.
IPSec VPN – a client software needs to be installed on client machines. Usually implemented for access to entire network.
Deemed to be more secured. But costs more due to client software licensing.
To Become Certified For CISSP Please Visit This Link;







