[bs_icon name=”glyphicon glyphicon-chevron-right”] Introduction To Network
Monthly Archives:: January 2016
CompTIA Network+ | Microsoft MTA Networking: Properties of Routing
[bs_icon name=”glyphicon glyphicon-chevron-right”] The Purpose and Properties of Routing
CompTIA Network+ | Microsoft MTA Networking: Common IPv4 and IPv6 Routing Protocols
Common IPv4 and IPv6 Routing Protocols
CompTIA Network+ | Microsoft MTA Networking: Addressing Technologies
Proper Use of Addressing Technologies
CompTIA Network+ | Microsoft MTA Networking: IP Address Formats
Identify the Following Address Formats
CompTIA Network+ | Microsoft MTA Networking: Command Line Interface Tools
Traceroute – A command-line troubleshooting tool that enables you to view the route to a specified host. This will show how many hops the packets have to travel and how long it takes. In Windows operating systems, the command used is “tracert”.
CompTIA Network+ | Microsoft MTA Networking: Common Networking Protocols
Common Networking Protocols
CompTIA Network+ | Microsoft MTA Networking: Troubleshooting
Here are the steps for troubleshooting a network
CompTIA Sec+ | Microsoft MTA Security: Remote Access
One of the most ever-present and ancient uses of the Internet and networking has been to provide remote access to networks or network resources.
CompTIA Sec+ | Microsoft MTA Security: kinds of attacks
A key aspect to any war is to know your enemy. If you consider the battle against malicious users a war, then understanding the attacks that they use is crucial.
CompTIA Sec+ | Microsoft MTA Security: Incident response
Incident response [bs_icon name=”glyphicon glyphicon-chevron-right”] Concept and procedures
CompTIA Sec+ | Microsoft MTA Security: Protocols
SNMP: It (SNMP) is a mainstream convention for system administration. It is utilized for gathering data from, and designing, system gadgets, for example, servers, printers, centers, switches, and switches on an Internet Protocol (IP) system.
CISSP Access Control Models
Data access controls are established to control how subjects can access data, what they can access with it, and what they can do with it once accessed. Three primary types of access control are discussed in this section. [bs_icon name=”glyphicon glyphicon-chevron-right”] Mandatory Access Control (MAC)
CISSP Legal Systems
The two law systems that form the basis of legal systems in most countries are:
CISSP Kerberos
Kerberos is a network authentication protocol created by the Massachusetts Institute of Technology (MIT) that uses secret-key cryptography. Kerberos has three parts: a client, server, and trusted third party (KDC) to mediate between them.
CISSP Attacks
[bs_icon name=”glyphicon glyphicon-chevron-right”] Types of Attacks Denial of Service (DoS) Smurf Fraggle SYN Flood Teardrop Distributed Denial of Service (DDoS) Ping Sweep Port Scan Salami attack Man-in-the-Middle Session or TCP Hijacking Replay Buffer Overflow Scareware and Ransomeware Password attack Covert channels [bs_icon name=”glyphicon glyphicon-chevron-right”] Web Attacks SQL Injection – An injection of SQL query through input… Read more »
CISSP Asymmetric Systems
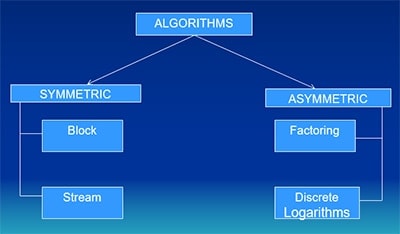
Asymmetric Systems –Uses a pair of keys (private and public) for encryption and decryption
CompTIA Network+ | Microsoft MTA Networking: TCP/UDP Ports
Identify Commonly Used TCP/UDP Ports
CompTIA Sec+ | Microsoft MTA Security: CIA

What’s CIA?
Cisco CCNA Extended Access List
Follow @ASM_Educational Cisco CCNA-Extended access list In this Lab we will cover the concept of Extended ACL , make sure read another blogs about Standard ACL .
Cisco CCNA Standard Access List
Follow @ASM_Educational Click here to read the presentation Cisco CCNA-Standard access list There are two kinds of ACL:
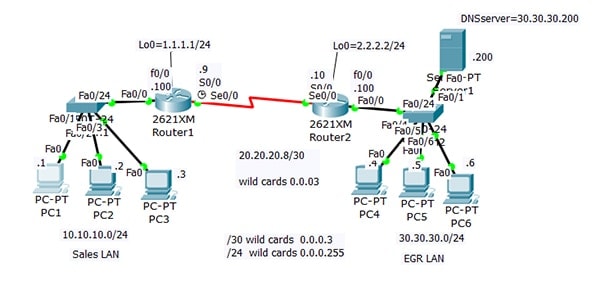
Cisco CCNA OSPF and Wild Card Part 2
Follow @ASM_Educational seated at PC1 =10.10.10.1 I can not ping 30.30.30.6
Cisco CCNA OSPF and Wild Card Part 1
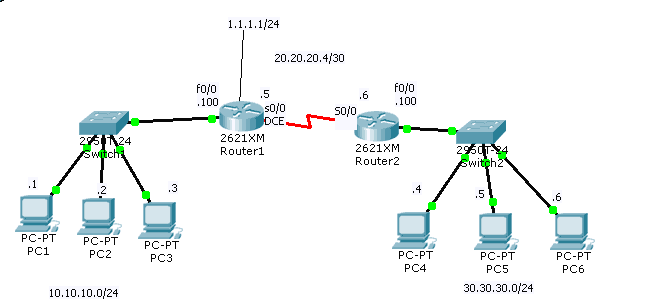
Follow @ASM_Educational Wild cards are very important in OSPF
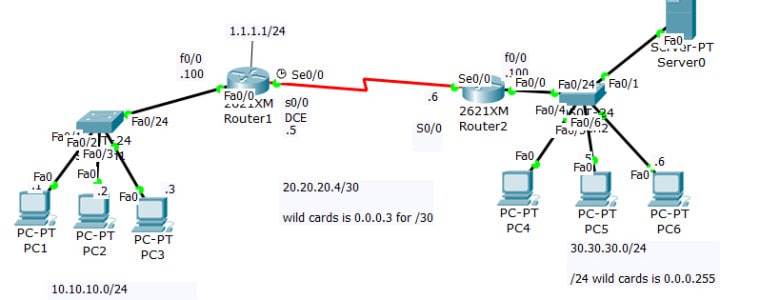
Cisco CCNA Video Training- DHCP Server
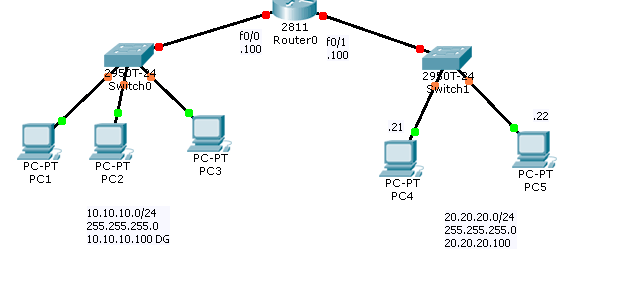
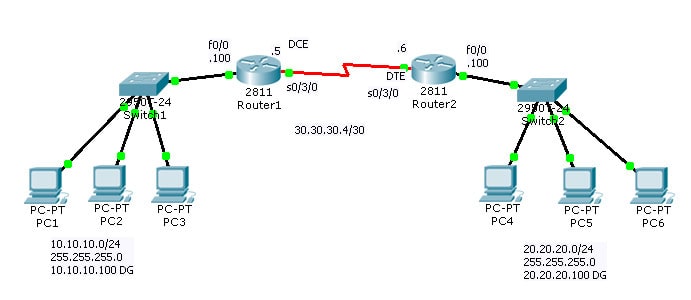
Follow @ASM_Educational In this lab we are trying to make our Cisco Router Act as a DHCP server , that is R1 will give ip address 10.10.10.0/24 to left side Pc and it will give the IP address 20.20.20.0/24 to right side of PC. The Goal is Prepare you for your Cisco CCNA Certification exam.
CompTIA A+ | Microsoft MTA O/S: Authentication
Authentication : The verification of a person’s identity – Helps protect against unauthorized access.
CompTIA A+ | Microsoft MTA O/S: Types of Optical Discs
Optical disc drives use removable media to store and retrieve data, typically 5.25”.
CompTIA A+ | Microsoft MTA O/S: Troubleshooting Tips
No network connectivity?
CompTIA A+ | Microsoft MTA O/S: Storage Devices
Hard Disk Drives are nonvolatile (meaning they don’t lose data when power off) devices that store data, generally 3.5”. Types of HDD include:
CompTIA A+ | Microsoft MTA O/S: RAID
RAID stands for Redundant Array of Inexpensive Disks. RAID 0 is striping, RAID 1 is mirroring , RAID 5 is striping with parity, RAID 10 is mirrored sets in a striped set. [bs_icon name=”glyphicon glyphicon-arrow-right”] RAID 0 is not fault-tolerant. If RAID 1 uses two disk controllers, it is disk duplexing. … Read more »
CompTIA A+ | Microsoft MTA O/S: Sound cards

Sound cards connect as x1 PCIe or PCI cards and normally have PC 99 color-coded 1/8” mini-jacks for I/O and speakers, and optical I/Os known as S/PDIF (example: TOSLINK). Alternatively referred to as an audio output device, sound board, or audio card. A sound card is an expansion card or IC for producing sound… Read more »
CompTIA A+ | Microsoft MTA O/S: Video cards
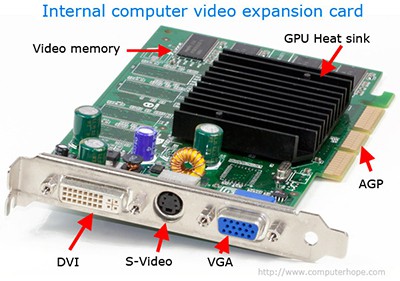
Video cards connect to motherboards by way of x16 PCIe (most common, typically black), AGP (brown), or PCI (white) expansion slots.
CompTIA A+ | Microsoft MTA O/S: Random Access Memory (RAM)
Random Access Memory (RAM) types include SDRAM, DDR, DDR2, DDR3, RDRAM and SODIMMs.
CompTIA A+ | Microsoft MTA O/S: CPU
The Central Processing Unit (CPU) or processor takes care of all calculations.
CompTIA A+ | Microsoft MTA O/S: Motherboards

Motherboards – Connect everything together. Typical form factors include ATX (most common), microATX, ITX, and BTX.
Students Exam Reports
Here are ASM Students who has taken ,CompTIA ,Cisco ,CCNA, CCNP ,Microsoft ,MCSA Exam. We are proud of them.
Students Testimonials CompTIA
Cisco CCNP Switch ARP Inspection
Dynamic ARP Inspection (DAI) is a security feature that fixes some well-known weaknesses in the ARP protocol.
CCNP Port Security
In order to Prevent Man-In-Middle Attack we will use Port Security (for Example to secure Port f0/3)
Community Outreach – Feb 14,2016

Please Join us for this Homeless Outreach on Sunday 2/14/2016 at Rockville MD.
Community Outreach – Jan 10,2016

Please Join us for this Homeless Outreach on Sunday 1/10/2016 at Rockville MD.
CCNP DHCP Snooping
DHCP Snooping is used to block untheorized DHCP server.
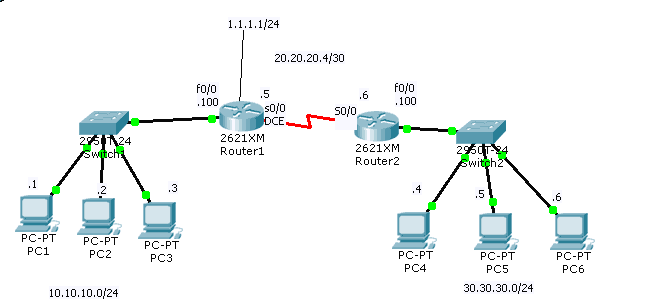
Cisco CCNA Video Training- Static Route
Follow @ASM_Educational In this lab we are showing the concept of Cisco Static Route , so it would prepare you for Cisco CCNA Certification.
Blogs
Search our blog. Welcome to ASM Blogs . For your convenience we offer the Exam cram and Tips in different formats. Please feel free to contact us about our blogs or courses Notes & Cisco CCNA Exam Notes & Tips Cisco CCNP Exam Notes & Tips Juniper JNCIA Exam Notes & Tips CompTIA A+ Exam Notes &… Read more »
Basic Cisco Router Configuration Password
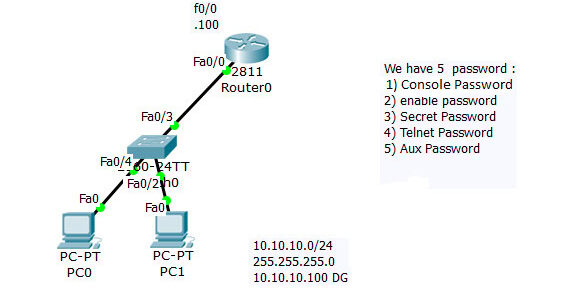
Follow @ASM_Educational In here we are covering basic Cisco CCNA Password Router Configuration.







