[bs_icon name=”glyphicon glyphicon-chevron-right”] The Role of Measurement Measurement plays a critical role within ITIL®, both as a part of Continual Service Improvement, but also within Service Level Management and as an essential part of all processes. Measurements can be used for four basic purposes as shown below:
Monthly Archives:: February 2016
Exin ITIL Service Operation Processes
[bs_icon name=”glyphicon glyphicon-chevron-right”] Incident Management Incident Management is concerned with the rapid restoration of services and with minimization of impact to the business.
Exin ITIL Service Operation
Service Operation [bs_icon name=”glyphicon glyphicon-chevron-right”] Overview The Service Operation phase of the Service Lifecycle is concerned with ensuring that services operate within agreed parameters. When service interruptions do occur, Service Operation is charged with restoring service as quickly as possible and with minimizing the impact to the business. [bs_icon name=”glyphicon glyphicon-chevron-right”] Business Value… Read more »
Exin ITIL Change Management
Service Transition Processes [bs_icon name=”glyphicon glyphicon-chevron-right”] Change Management Change Management is concerned with recording, evaluating, approving, testing, and reviewing changes to services, systems, and other Configuration Items.
Exin ITIL Concepts and Models
[bs_icon name=”glyphicon glyphicon-chevron-right”] Change Authority In ITIL® the entity charged with approval of a Request for Change is called the Change Authority.
Exin ITIL IT Security Management
IT Security Management is the process concerned with the protection of IT assets (including services) from security threats.
Exin ITIL Concepts and Models – Change Types
[bs_icon name=”glyphicon glyphicon-chevron-right”] Normal Changes are changes which meet predefined criteria that qualify them for handling via the Normal Change Management process.
Exin ITIL The Four P’s of Service Design
The ‘Four P’s of Service Design’ represent areas which should be taken into consideration when designing a service.
Exin ITIL Capacity Management
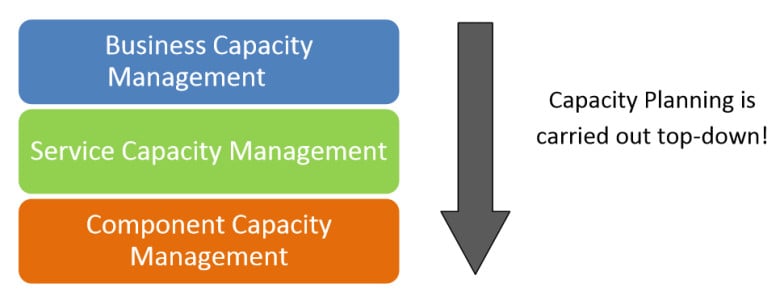
Capacity Management is concerned with ensuring that cost-effective capacity exists at all times which meets or exceeds the agreed needs of the business as established in Service Level Agreements.
Exin ITIL The RACI Model
ITIL also utilizes the RACI model as a generic tool for reviewing and assigning four key roles to any important task or activity.
Exin ITIL Foundation Service Desk
The Service Desk provides a single point of contact between users and the IT organization.
CompTIA Network+ | Microsoft MTA Networking: Common Logical Network Topologies
[bs_icon name=”glyphicon glyphicon-chevron-right”] Peer to Peer – A peer to peer network is one in which lacks a dedicated server and every computer acts as both a client and a server.
CompTIA Network+ | Microsoft MTA Networking: LAN Technology Types and Properties
Ethernet – Ethernet is the most widely-installed local area network ( LAN) technology.
CompTIA Network+ | Microsoft MTA Networking: WAN Technology Types and Properties
[bs_icon name=”glyphicon glyphicon-chevron-right”] Frame Relay – Frame relay is a secure, private network that utilizes a logical path or “virtual circuit” to allocate bandwidth for high performance transmissions.
CompTIA Network+ | Microsoft MTA Networking: Wiring Standards
568A and 568B – The number 568 refers to the order in which the individual wires inside a CAT 5 cable are terminated.
CompTIA Network+ | Microsoft MTA Networking: Standard Cable Types and Their Properties
Cable Types :
CompTIA Network+ | Microsoft MTA Networking: Characteristics of Wireless Standards
Wireless networks allow computers to comunicate without the use of cables using IEEE 802.11 standards, also known as Wi-Fi.
CompTIA Sec+ | Microsoft MTA Security: Firewall
[bs_icon name=”glyphicon glyphicon-chevron-right”] What is a Firewall? A firewall is any hardware or software designed to prevent unwanted network traffic. Some firewalls are simplistic in nature;
CompTIA Sec+ | Microsoft MTA Security: Cryptography
[bs_icon name=”glyphicon glyphicon-chevron-right”] Introduction to Cryptography
CompTIA Sec+ | Microsoft MTA Security: Malicious Software
Viruses, Trojan Horses, Worms Despite all the hype about viruses and worms, the Security+ exam actually does not heavily test on viruses and the like.
CISSP Computer System Architecture
Computer System Architecture At the core of every computer system is the CPU and hardware that make it run.
CISSP Penetration Testing
Penetration testing is a series of activities undertaken to identify and exploit security vulnerabilities.
CompTIA Sec+ | Microsoft MTA Security: Tunneling
Tunneling, VPN, and IPSec
CISSP Single sign-on
Single sign-on is an attempt to address a problem that is common for all users and administrators.
CISSP Intrusion-Detection Systems (IDS)
An IDS is designed to function as an access-control monitor. It can monitor network or host activity and record which users attempt to access specific network resources.
CompTIA A+ | Microsoft MTA O/S: Types of Networks
Exam Cram: LAN = Local Area Network WAN = Wide Area Network MAN = Metropolitan (or Municipal) Area Network PAN = Personal Area Network
CompTIA A+ | Microsoft MTA O/S: Types of Custom PCs
[bs_icon name=”glyphicon glyphicon-chevron-right”] Custom PCs include: Audio/Video workstations – needs special A/V cards, fast hard drives and multiple monitors
CompTIA A+ | Microsoft MTA O/S: 7 Tips for Effective Study Habits
#1 DON’T CRAM #2 DO PLAN #3 TAKE A BREAK #4 MIX IT UP #5 PICK YOUR TOPICS #6 FIND PRACTICE TESTS #7 USE TEST PREP MATERIALS
CompTIA A+ | Microsoft MTA O/S: Wireless encryption protocols
Wireless encryption protocols include :
CompTIA A+ | Microsoft MTA O/S: Switch and Router and Firewall
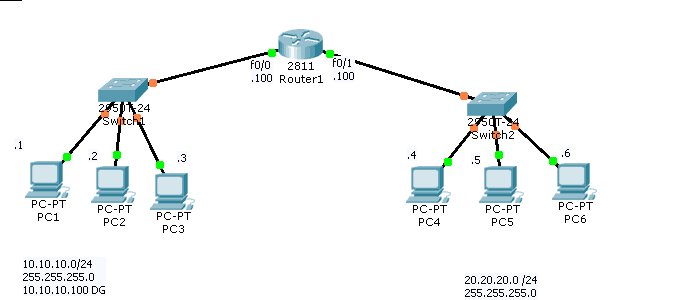
Switches connect computers together in a LAN.
CompTIA A+ | Microsoft MTA O/S: ATX
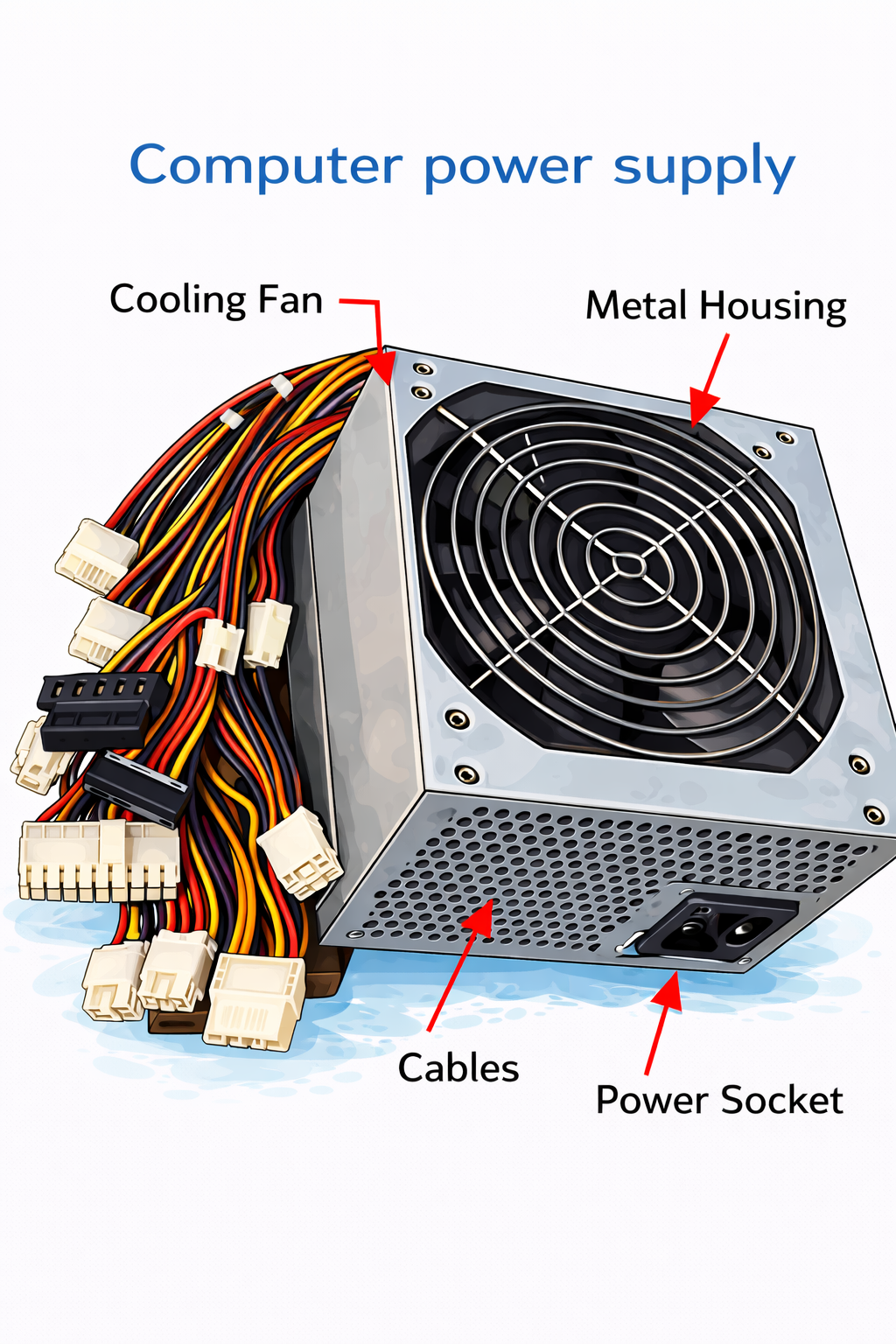
ATX 12V 2.x Power Supplies connect to the motherboard by way of 24-pin cable + 4-pin for CPU and 6 or 8-pin for video. Advantages of the ATX motherboard The ATX motherboard includes advanced control facilities, where the BIOS program continually checks the CPU temperature and voltages, the cooling fans RPM, etc. If overheating occurs,… Read more »
CompTIA A+ | Microsoft MTA O/S: IPv4 and IPv6
IPv4 addresses are 32 bit dotted-decimal numbers (like 192.168.1.1) and can be statically (manually) inputed or dynamically (automatically) assigned by DHCP.
CompTIA A+ | Microsoft MTA O/S: 6-Step Troubleshooting Process
CompTIA 6-Step Troubleshooting Process:
CompTIA A+ | Microsoft MTA O/S: USB
Short for Universal Serial Bus, USB (pronounced yoo-es-bee) is a plug-and-play interface that allows a computer to communicate with peripheral and other devices.
Cisco CCNA Basic Router Configuration
Follow @ASM_Educational Here are the configuration for Basic Router Configuration When You Open a new router you will see Router> This is called user mode; then you type en=enable to get to enable mode Router# This is called privilege mode
6 Cisco CCNA Switch Tips
Follow @ASM_Educational Get our complete tutorial in PDF To Find Out If Link is UP Switch#show ip int brief
9 Cisco CCNA Router Tips

Follow @ASM_Educational Get our complete tutorial in PDF To Find out if link is up and has Ip address Router#show ip int brief
ASM Student’s Practical Video Lab
[bs_icon name=”glyphicon glyphicon-expand”] Here is ASM’s A+ Bootcamp Students practical video lab. They are building a brand new PC as a part of their training program (Computer Cost is included in tuition). To Become Certified For CompTIA A+ Please Visit This Link ;







