The Types of Wireless Attacks Part 1

CompTIA Security+ Objective 1.2
Replay Attacks
A replay attack occurs when an attacker copies a stream of messages between two parties and replays the stream to one or more of the parties. Unless mitigated, the computers subject to the attack process the stream as legitimate messages, resulting in a range of bad consequences, such as redundant orders of an item.
How to prevent a replay attack
Preventing such an attack is all about having the right method of encryption. Encrypted messages carry “keys” within them, and when they’re decoded at the end of the transmission, they open the message. In a replay attack, it doesn’t matter if the attacker who intercepted the original message can read or decipher the key. All he or she has to do is capture and resend the entire thing — message and key — together.
To counter this possibility, both sender and receiver should establish a completely random session key, which is a type of code that is only valid for one transaction and can’t be used again.
Another preventative measure for this type of attack is using timestamps on all messages. This prevents hackers from resending messages sent longer ago than a certain length of time, thus reducing the window of opportunity for an attacker to eavesdrop, siphon off the message, and resend it.
Another method to avoid becoming a victim is to have a password for each transaction that’s only used once and discarded. That ensures that even if the message is recorded and resent by an attacker, the encryption code has expired and no longer works.
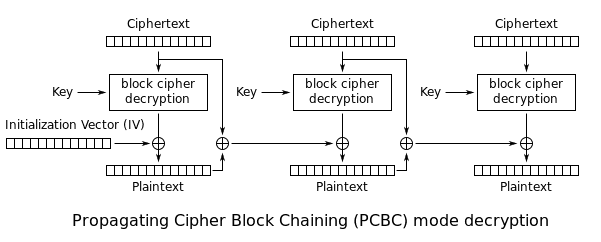
Initialization vector (IV) Attack
An initialization vector (IV) attack is an attack on wireless networks. It modifies the IV of an encrypted wireless packet during transmission. IVs are blocks of bits that are used to differentiate users on the wireless network. IVs eliminate the need for users to constantly reauthenticate with an access point and are therefore sent frequently. Eventually, an authenticated user will reuse an IV because the number of bits used is limited; the frequency of repetition depends on how much data is sent across the connection.
If enough IVs are captured, it is possible to decipher the encryption key using a program, such as aircrack-ng. Once an attacker learns the plaintext of one packet, the attacker can compute the RC4 key stream generated by the IV used. This key stream can then be used to decrypt all other packets that use the same IVs. Since there is only a small set of possible initialization vectors, attackers can eventually build a decryption table to decrypt every packet sent over that wireless connection.
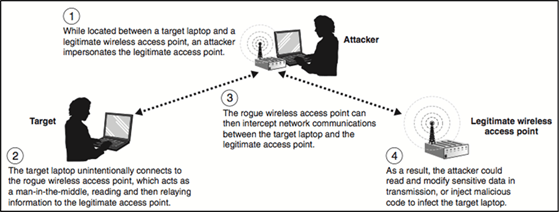
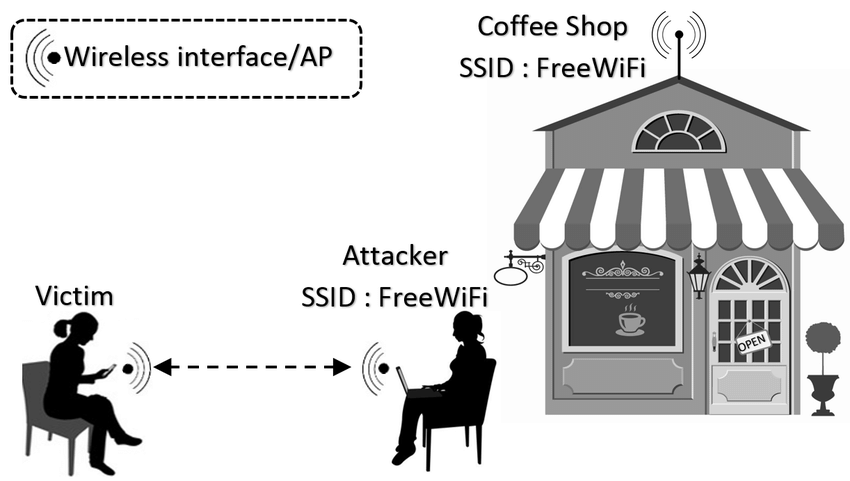
Evil Twin
An evil twin, in security, is a rogue wireless access point that masquerades as a legitimate Wi-Fi access point so that an attacker can gather personal or corporate information without the end-user’s knowledge.
An attacker can easily create an evil twin with a smartphone or other Internet-capable device and some easily-available software. The attacker positions himself in the vicinity of a legitimate hot spot and lets his device discover what service set identifier (name) and radio frequency the legitimate access point uses. He then sends out his own radio signal, using the same name as the legitimate access point.
To the end-user, the evil twin looks like a hot spot with a very strong signal; that’s because the attacker has not only used the same network name and settings as the “good twin” he is impersonating, he has also physically positioned himself near the end-user so that his signal is likely to be the strongest within range. If the end-user is tempted by the strong signal and connects manually to the evil twin to access the Internet, or if the end-user’s computer automatically chooses that connection because it is running in promiscuous mode, the evil twin becomes the end-user’s Internet access point, giving the attacker the ability to intercept sensitive data such as passwords or credit card information.
Evil twins are not a new phenomenon in wireless transmission. Historically they have been called base station clones or honeypots. What’s different now is that more businesses and consumers are using wireless devices in public places and it’s easier than ever for someone who doesn’t have any technical expertise to create an evil twin.
How to Prevent an Evil Twin
To avoid evil twin network connections, end users should only use public hot spots for Web browsing and refrain from online shopping or banking. To protect your individual or corporate data, individual who use wireless devices should always connect to the Internet through a VPN.
Rogue Access Point
One of the most common wireless security threats is the rogue access point—it is used in many attacks, both DoS and data theft. Many other rogue access points, however, are deployed by employees wanting unfettered wireless access—these access points are called soft access points. Other rogues are located in neighboring companies using your network for free access.
Typically low-cost and consumer-grade, these access points often do not broadcast their presence over the wire and can only be detected over-the-air. Because they are typically installed in their default mode, authentication and encryption are not enabled, thereby creating a security hazard. Because wireless LAN signals can traverse building walls, an open access point connected to the corporate network the perfect target for war driving. Any client that connects to a rogue access point must be considered a rogue client because it is bypassing the authorized security procedures put in place by the IT department.
How to Prevent an Attack from a Rogue Access Points?
Establish strict rules and make sure they are well published.
Only authorized IT staff can connect networking equipment. All devices that connect to the network, including wireless access points, conform to company security policies.
Note: Some colleges even expel students who are caught with rogue access points or ad-hoc networks.
Change the rogue classification rules.
By default, unknown devices are classified as suspects. When you change this default to rogue, the controller automatically classifies any third-party access point or client as a rogue, and you can optionally isolate the access point by dropping all packets to and from the device.
Eliminate benign access points from the rogue list so that real rogues stand out.
When you add safe networks’ SSIDs and/or vendor names to the list of SSIDs allowed on the network, these access points cannot be classified as rogues. .
Use strong security
The IEEE 802.11i security standard uses IEEE 802.1X for mutual authentication between the network and the client. This means that clients that try to access network resources must be authenticated by the network. In a similar vein, the client verifies the authenticity of the network infrastructure it is attaching to before beginning data transmission. With 802.1X, the credentials used for authentication, such as login passwords, are never transmitted without encryption over the wireless medium. In addition, 802.1X provides dynamic per-user, per-session encryption keys, removing the administrative burden and security issues associated with static encryption keys. Security is configured in WLAN profiles.
Use active access point scanning in addition to passive scanning.
Active scans send probes with a null SSID name to look for rogue access points and clients. Active scan is enabled by default on radio-profiles. We recommend that you do not change this setting.
Immediately investigate wireless bridge frames and eliminate the source.
An attacker often sets up a laptop with two wireless adaptors—one card is used by the rogue access point and the other is used to forward requests through a wireless bridge to the legitimate access point.
Enable automatic countermeasures to immediately react to rogues or suspect rogues.
Countermeasures can attack or isolate rogue and/or suspect transmitters using various methods of attack.
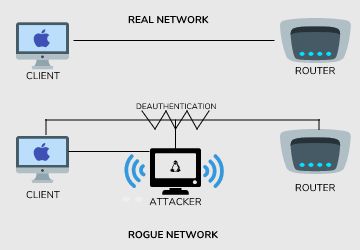
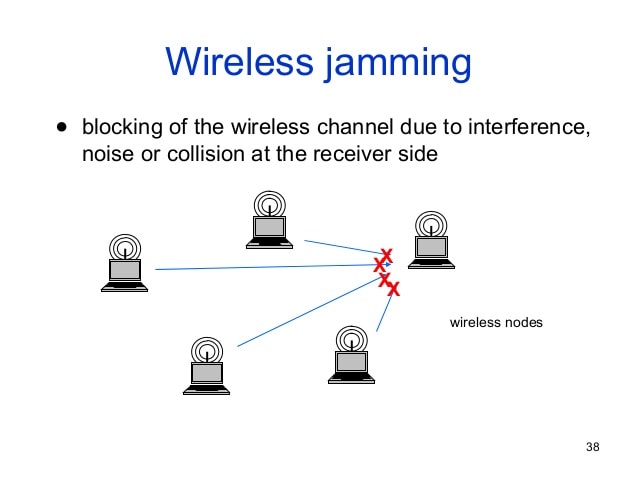
Jamming
There’s nothing really good that comes from wireless jamming. This is jamming the radio frequencies of a communication, most commonly for a wireless network. At its most basic level, this is a denial of service. You are trying to use a network that is no longer available, so you don’t have access to any of those services. The goal with radio frequency jamming is to decrease the signal-to-noise ratio at the receiving device.
Because there’s so much jam signal, the device isn’t able to discern the good signal. And therefore, you aren’t able to communicate at all over the network.
Networks can also be jammed by flooding the AP with Deauthentication Frames in what is know as a deauth-attack. By assuming the identity (MAC address) of a station on the network, the AP will deauthenticate the real station. The real station will then attempt to reauthenticate, but, it will never succeed due to the barrage of deauth-frames and its network access will be effectively blocked.
How to minimize the impact of Jamming?
To minimize the impact of an unintentional disruption, it is important the identify its presence. Jamming makes itself known at the physical layer of the network, more commonly known as the MAC (Media Access Control) layer. The increased noise floor results in a faltered noise-to-signal ratio, which will be indicated at the client. It may also be measurable from the access point where network management features should able to effectively report noise floor levels that exceed a predetermined threshold. From there the access points must be dynamically reconfigured to transmit channel in reaction to the disruption as identified by changes at the physical layer.
Source: Tutorialspoint







