A local area network (LAN) is a critical component of a modern data network. A LAN is comprised of one or more computers, a communication protocol, a network topology, and cabling or a wireless network to connect the systems.
A LAN is best defined as computers or other devices that communicate over a small geographical area such as the following:
- A section of a one-story building
- The whole floor of a small building
- Several buildings on a small campus
LAN Communication Protocols
More than 80% of all LANs use the Ethernet protocol as a means of communication. The Ethernet specification describes how data can be sent between computers in physical proximity. The DIX (Digital, Intel, and Xerox) group first released Ethernet in 1975. Since its introduction, the IEEE Standards Committee has introduced several variations of the Ethernet II protocol, including these:
- IEEE 802.3
- IEEE 802.3 with Logical Link Control (LLC)
- IEEE 802.3 with Subnetwork Access Protocol (SNAP)
Although the CISSP exam will not delve very far into the specifics of Ethernet, it is interesting to note the size and structure of these frames. An Ethernet frame is from 64 to 1,518 bytes. The Ethernet frame itself uses 18 bytes for control information; therefore, the data in an Ethernet frame can be between 46 and 1,500 bytes long.
The second most popular LAN networking protocol is Token Ring, which functions by arranging all the systems in a circle. A special packet, known as a token, travels around the circle. If any one device needs to send information, it must capture the token, attach a message to it, and then let it continue to travel around the network.
Network Topologies
The design layout of a network is its topology. Before a network can be installed, a topology must be chosen to match its needs and intended use. Common topologies include bus, star, and ring; each is discussed next.
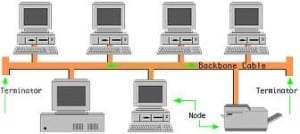
Bus Topology
A bus topology consists of a single cable with multiple computers or devices attached to it. This cable is terminated on each end. In large environments, this is impractical because the medium has physical limitations. These problems can run the range from low speeds to network outages: One break can bring down the entire network (see Figure 6.1).
Star Topology
This is the oldest of the three primary network topologies and was originally used in telephone systems. The design of a star network consists of multiple computers or devices attached to a central hub. Wires radiate outward from the hub in a starlike pattern. Although this scheme uses the most cable, a break will most like affect only one computer. This is the most widely used LAN topology (see Figure 6.2).

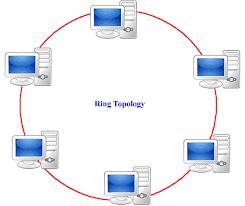
Ring Topology
The ring topology is characterized by the fact that there are no endpoints or terminators. Its layout is that of a continuous loop of cable in which all networked computers are attached. Token Ring and Fiber Distributed Data Interface (FDDI) networks use a ring topology (see Figure 6.3).
LAN Cabling
Even with a defined topology, it is necessary to determine what type of cable will connect the various devices. Cables carry the electrical signal between the devices. One of two transmissions methods is used: baseband or broadband. Baseband transmissions use a single channel to communicate. Ethernet uses a baseband transmission scheme. Broadband uses many channels and frequencies. Two good examples of broadband are cable television and digital subscriber lines (DSL).
Many types of cables can be used for network communications, including coaxial (coax), twisted-pair, and fiber:
- Coaxial cable- Coax cable consists of a single solid-copper wire core that uses a braided shield for the second conductor. Both conductors are covered with a plastic or insulative coating. Although it was widely used in the early days of networking, its usage has waned.
- Twisted pair- If you’re in an office, you will probably notice that twisted-pair wiring is being used to connect your computer to a wall jack located nearby. The most common connector is the RJ-45. Twisted pair can be purchased in a multitude of varieties, one of which is unshielded twisted pair (UTP). UTP is unshielded copper wire insulated in plastic that is twisted together. Not only is it easy to work with, but it also is generally inexpensive. The primary drawback to copper cabling is that it is vulnerable to being tapped and emanates electrical energy, which could possibly be intercepted. Table 6.1 specifies many common table types, lengths, and topologies.
| Ethernet Name | Cable Specifications | Distance Supported | Topology |
|---|---|---|---|
| 10BASE-5 | 50-ohm, thick coaxial (Thicknet) | 500m | Bus |
| 10BASE-2 | 50-ohm, RG-58 A/U (Thinnet) | 185m | Bus |
| 10BASE-T | Cat3 UDP (or better) | 100m | Star |
| 10BASE-FL | Multimode fiber optic | 2,000m | Star |
| 100BASE-TX | Cat5 UTP | 100m | Star |
| 100BASE-T4 | Cat3 UTP (or better) | 100m | Star |
| 100BASE-FX multimode fiber optic | Multiple-fiber connections | 136 meters | Star |
| 100BASE-FX multimode fiber optic | One-fiber connection | 160 meters | Star |
[bs_icon name="glyphicon glyphicon-exclamation-sign"] For the exam, you will want to know that plenum-grade cable is coated with a fire-retardant coating and is designed to be used in crawlspaces, in false ceilings, and below raised floors in a building. This special coating is designed to not give off toxic gasses or smoke as it burns, to help ensure the safety of occupants in case of fire.
Fiber-optic cable- Whereas twisted pair and coax rely on copper wire for data transmissions, fiber uses glass. These strands of glass carry light waves that represent the data being transmitted. Basically two types of fiber cables are in use. They are constructed differently to handle different types of light:
- Multimode fiber- Typically used in LANs and powered by LEDs
- Single-mode fiber- Typically used in WANs and powered by laser light
[bs_icon name="glyphicon glyphicon-exclamation-sign"] You will want to remember that fiber is more secure than copper cable because it does not radiate signals and is extremely difficult to tap.
802.11 Wireless Networking
When is a cable not a cable? When you use wireless for connectivity. Wireless networks have become popular because of their low cost and convenience. It’s so much easier to plug in a wireless access point (WAP) than to run 1,000 feet of cable. Currently, the standard for wireless networks is 802.11 wireless, which is handled by the Institute of Electrical and Electronic Engineers (IEEE). Although it is not quite as robust as a wired network, 802.11 wireless equipment is generally fast and efficient. There are three primary types:
- 802.11a- This version operates in the 5.15?5.35GHz to 5.725?5.825GHz frequency range and can support speeds of up to 54Mbps.
- 802.11b- Operates in the 2.4000?2.2835GHz frequency range and can reach speeds of up to 11Mbps.
- 802.11g- This popular standard operates in the 2.4GHz frequency range and can support speeds up to 54Mbps.
In North America, 802.11 supports 11 channels. The channel designates the frequency on which the network will operate. European units support 13 channels. Most wireless devices broadcast by using spread-spectrum technology. This method of transmission transmits data over a wide range of radio frequencies. Spread-spectrum technologies include frequency-hopping spread spectrum, an older technology, and sequence spread spectrum. Spread spectrum lessens noise interference and allows data rates to speed up or slow down, depending on the quality of the signal. Obstructions such as walls, doors, and other solid objects tend to block or reduce signal strength.
Unfortunately, many end users who are moving to wireless don’t have any appreciation of the security measures they should employ. Using wireless requires little more than powering up the access point and plugging in an active RJ-45 jack.
So, what are some of the technologies used to protect wireless? Originally, there was Wired Equivalent Privacy (WEP), which the IEEE implemented at the data link layer. WEP encrypts data with the RC4 encryption algorithm. The key was limited to 40 bits because of export rules that existed during the late 1990s when the 802.11 protocol was being developed. This provides a very limited level of encryption that is relatively easy to compromise by someone with even a modest understanding of the problem. One way the industry responded to this potential problem was by incorporating 802.1x into many wireless devices. 802.1x provides port-based access control. When used in conjunction with extensible authentication protocol (EAP), it can be used to authenticate devices that attempt to connect to a specific LAN port.
WEP’s sucessor was WiFi Protected Access (WPA). WPA uses Temporal Key Integrity Protocol (TKIP). TKIP scrambles the keys using a hashing algorithm and adds an integrity-checking feature that verifies that the keys haven’t been tampered with. In 2004, the IEEE approved the next upgrade to wireless security, WPA2. It is officially known as 802.11.i. This wireless security standard makes use of the Advanced Encryption Standard (AES). Don’t be surprised to see key sizes of up to 256 bits, which is a vast improvement over the original 40-bit encryption WEP used.
[bs_icon name="glyphicon glyphicon-exclamation-sign"] War driving is the practice of driving around, finding, mapping, and possibly connecting to open wireless networks. Tools such as Netstumbler, Kismit, and AirSnort are used to aid the wardriver.
Bluetooth
Bluetooth technology is designed for short-range wireless communication between mobile and handheld devices. Bluetooth started to grow in popularity in the mid- to late 1990s. Bluetooth was envisioned as a technology that would facilitate for the growth of personal area networks (PANs), which allow a variety of personal and handheld electronic devices to communicate. For example, in a PAN, a cellphone could communicate with a personal digital assistant (PDA) and a laptop. Bluetooth will allow these devices to communicate as they come in range of each other or are activated. The three classifications of Bluetooth are as follows:
- Class 1- This classification has the longest range (up to 100m) and has 100mW of power.
- Class 2- Although this classification is not the most popular, it allows transmission of up to 20m and has 2.5mW of power.
- Class 3- This is the most widely implemented classification. It supports a transmission distance of 10m and has 1mW of power.
Although Bluetooth does have some built-in security features, it has been shown to be vulnerable to attack. At a recent DEFCON security conference, security professionals demonstrated ways to sniff Bluetooth transmissions from up to a half-mile away. Bluetooth operates at a frequency of 2.45GHz and divides the bandwidth into narrow channels to avoid interference with other devices that use the same frequency.
**Source by wikipedia**
To Become Certified For CISSP Please Visit This Link;







