Amazon AWS S3 Endpoint
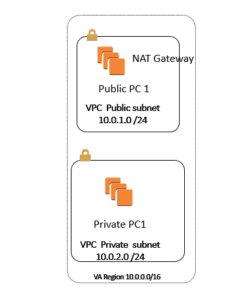
In Here we have One VPC =10.0.0.0/16 also we have three Subnet as follow
10.0.1.0/24 Public Subnet1
10.0.2.0/24 Private Subnet2
10.0.3.0/24 Public Subnet3
I have two server one is called Public1 inside the Public Subnet=10.0.1.0/24 with
Public Ip address: 34.201.13.154
Private Ip address = 10.0.1.183
Password -LphUKwynw9
I have another server in Private Subnet 2= 10.0.2.0/24
Private Ip address = 10.0.2.248
Password = rSB=zj6(EY
Step 1) I logon the PC called Public1 and rename it to Public1
Step 2) Since I can not access the Server located in Private subnet; first I need to RDP to Public1, then from that Server, I will do RDP to Private Server =
So I will RDP to Ip address =10.0.2.248
Step 3) Make sure from the server called Public1 I can ping 10.0.2.248, then try to RDP to PC called Private1=10.0.2.248 then rename the PC to Private1, so this way you will not get confused which one is which.
Step 4) In order to be able to use the AWS CLI command line, you need to make sure to install the AWS CLI commands on the server.
Step 5) here is the CLI command line for Windows
https://docs.aws.amazon.com/cli/latest/userguide/awscli-install-windows.html#install-msi-on-windows
Step 6) Since I want to show how you can connect to S3 from CLI; after installing the CLI; we need to make sure the Server has the IAM Role ( since we do not want to put the credentials inside the Instance
Step 7) Go to IAM and create a Role called S3Admin Role.
Step 8) Now go back to both EC2 instance ( Public and Private ) and make sure you assign the IAM roles to them.
Step 9) Now when I go to Public Server and I Type at command Prompt I type AWS S3 LS I will be able to see all y buckets:
C:\Users\Administrator>aws s3 ls
2018-01-28 21:21:01 asmtest4568
2018-01-28 21:20:31 test12345asm
2018-01-28 21:20:47 test698932asm
2018-01-08 17:51:16 testasm12345
Step 10)Now we come to our main Problem; that is goal is to make the Private PC that is located inside the Private Subnet be able to connect to S3 but via VPC S3 endpoint
Step 11) I want to make sure before we do above, we need to make sure the AWS CLI command line is installed on the PC=Private1 , so First I create a NAT gateway ( like what we did in the last Video) then I make sure pick Public Subnet ( 10.0.1.0/24) and then I configure the My Private RT is pointed to NAT gateway .
You will be able to ping 8.8.8.8 from Private1 after few mins.
Step 12) Now I go and Install the AWS CLI from the last link we had :
https://docs.aws.amazon.com/cli/latest/userguide/awscli-install-windows.html#install-msi-on-windows
Make sure in the same way you have given the Role to Public1, you would give to Private1 ( Role=S3admin) so that way you do not need the credentials.
C:\Users\Administrator>aws configure
AWS Access Key ID [None]:
AWS Secret Access Key [None]:
Default region name [None]: us-east-1
Default output format [None]: table
Step 12) after I finish installing AWS CLI on PC called Private1, I will remove the NAT gateway; so it will not have access to Internet then I will do Amazon VPC Endpoint S3
Step 13) Now I will remove NAT gateway from it.
Step 14) Now I will go on the Top go to VPC; then I will go to left side click on Endpoint, then click on create an Endpoint, now at the bottom middle pick the S3 and make sure in here pick Private Subnet
Hint: for Nat Gateway, make sure pick Public Subnet
For S3 Endpoint, make sure pick Private Subnet
Step 15) Here I will pick the Full access
Policy
Full Access – Allow access by any user or service within the VPC using credentials from any AWS accounts to any resources in this AWS service. All policies — IAM user policies, VPC endpoint policies, and AWS service-specific policies (e.g. Amazon S3 bucket policies, any S3 ACL policies) — must grant the necessary permissions for access to succeed.
Policy
Step 16) Now make sure the private Routing Table is pointed to this VPC-E as a routing table.
| 10.0.0.0/16 | local | Active | No |
| pl-63a5400a (com.amazonaws.us-east-1.s3) | vpce-d92aabb0 | Active | No |
Step 17) now and go and test it and it should work.







