Server Roles
CompTIA A+ Exam objectives 2.5
(Summarize the properties and purposes of services provided by networked hosts.)
What do server roles achieve?
Server roles allow there to be more convenient or efficient options of doing specific tasks, such as accessing the internet, or using the printer.
Here are the 9 different types covered by CompTIA:
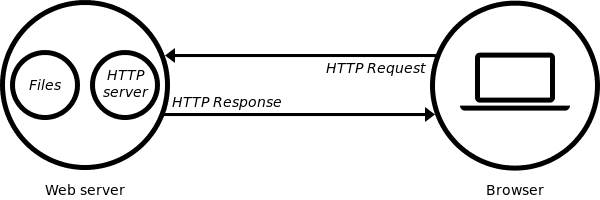
Web server
At the most basic level, whenever a browser needs a file which is hosted on a web server, the browser requests the file via HTTP. When the request reaches the correct web server (hardware), the HTTP server (software) accepts the request, finds the requested document (if it doesn’t then a 404 response is returned), and then sends it back to the browser, also through HTTP.
File server
A high-speed computer in a network that stores the programs and data files shared by it’s users. It acts like a remote disk drive. The difference between a file server and an application server is that the file server stores the programs and data, while the application server runs the programs and processes the data.
Print server
A computer in a network that controls one or more printers. The function is typically part of the operating system but may be an add-on utility that stores the print-image output from users’ machines and feeds it to the printer one job at a time. The computer and its printers are known as a “print server” or a file server with “print services.”
DHCP server
Dynamic Host Configuration Protocol (DHCP) is a network protocol that enables a server to automatically assign an IP address to a computer from a defined range of numbers (that is, a scope) configured for a given network.
DNS server
A dedicated server or a service within a server that provides DNS name resolution in an IP network. It turns names for websites and network resources into numeric IP addresses. DNS servers are used in large companies, in all ISPs and within the DNS system in the Internet, a vital service that keeps the Internet working. They are set up by network administrators and typically do not exist in the very small business or home.
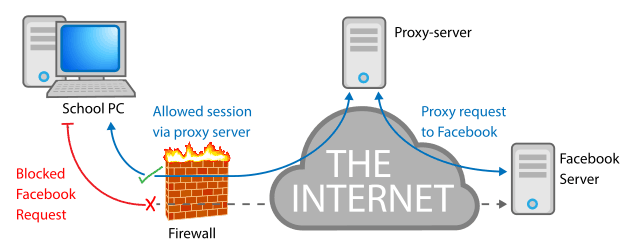
Proxy server
A proxy server, also known as a “proxy” or “application-level gateway”, is a computer that acts as a gateway between a local network (for example, all the computers at one company or in one building) and a larger-scale network such as the internet. Proxy servers provide increased performance and security.
A proxy server works by intercepting connections between sender and receiver. All incoming data enters through one port and is forwarded to the rest of the network via another port. By blocking direct access between two networks, proxy servers make it much more difficult for hackers to get internal addresses and details of a private network.
Mail server
A mail server (or email server) is a computer system that sends and receives email. In many cases, web servers and mail servers are combined in a single machine.
Authentication server
A device used in network access control. An authentication server stores the usernames and passwords that identify the clients logging in, or it may hold the algorithms for token access. For access to specific network resources, the server may itself store user permissions and company policies or provide access to directories that contain the information.
syslog
A protocol for transmitting event messages and alerts across an IP network. Messages are sent by the operating system or application at the start or end of a process or to report the current status of a process. Initially developed for the Unix sendmail application, syslog became commonly used in all environments and was made an IETF standard in 2001.
Learn more about our CompTIA A+ Certification







