Dynamic Host Configuration Protocol (DHCP)
Dynamic Host Configuration Protocol (DHCP) is a client/server protocol that automatically provides an Internet Protocol (IP) host with its IP address and other related configuration information such as the subnet mask and default gateway. In DHCP, port number 67 is used for the server and 68 is used for the client.
DHCP allows a network administrator to supervise and distribute IP addresses from a central point and automatically sends a new Internet Protocol (IP) address when a computer is plugged into a different place in the network.
DHCP is an application layer protocol that provides −
- Subnet Mask
- Router Address
- IP Address
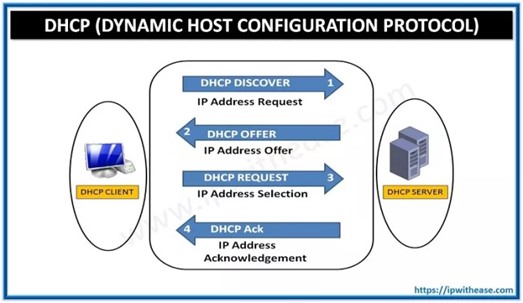
DHCP Client-Server Communication Diagram
In DHCP, the client and the server exchange DHCP messages to establish a connection.
DHCP Discover Message − Client Requests DHCP Information
- It is the first message produced by a client in the communication process between the client and server with the target address 255.255.255.255 and the source address 0.0.0.0.
- This message is produced by the client host to discover if there are any DHCP servers present in a network or not.
- The message might contain other requests like subnet mask, domain name server, and domain name, etc.
- The message is broadcast to all the devices in a network to find the DHCP server.

DHCP Offer Message − DHCP Server Offers Information to Client
- The DHCP server will reply/respond to the host in this message, specifying the unleashed IP address and other TCP configuration information.
- This message is broadcasted by the server.
- If there are more than one DHCP servers present in the network, then the client host accepts the first DHCP OFFER message it receives.
- Also, a server ID is specified in the packet to identify the server.
DHCP Request Message − Client Accepts DHCP Server Offer
- The Client receives the DHCP offer message from the DHCP server that replied/responded to the DHCP discover message.
- After receiving the offer message, the client will compare the offer that is requested, and then select the server it wants to use.
- The client sends the DHCP Request message to accept the offer, showing which server is selected.
- Then this message is broadcast to the entire network to let all the DHCP servers know which server was selected.
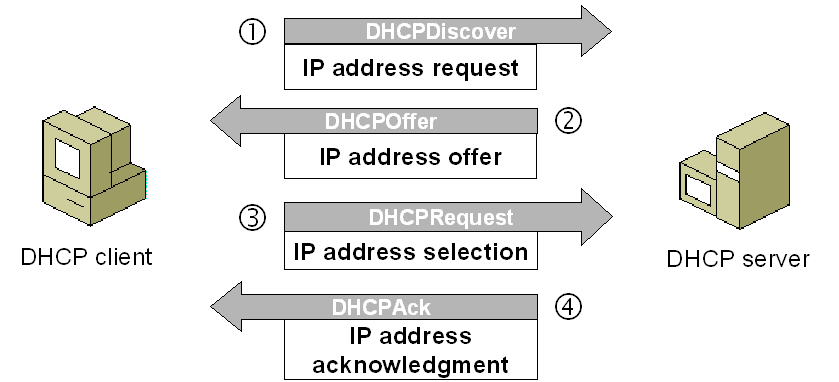
DHCP Acknowledgment Message − DHCP server acknowledges the client and leases the IP address.
- If a server receives a DHCP Request message, the server marks the address as leased.
- Servers that are not selected will return the offered addresses to their available pool.
- Now, the selected server sends the client an acknowledgment (DHCP ASK), which contains additional configuration information.
- The client may use the IP address and configuration parameters. It will use these settings till its lease expires or till the client sends a DHCP Release message to the server to end the lease.
DHCP Request, DHCP ACK Message − Client attempts to renew the lease
- The client starts to renew a lease when half of the lease time has passed.
- The client requests the renewal by sending a DHCP Request message to the server.
- If the server accepts the request, it will send a DHC ACK message back to the client.
- If the server does not respond to the request, the client might continue to use the IP address and configuration information until the lease expires.
- As long as the lease is still active, the client and server do not need to go through the DHCP Discover and DHCP Request process.
- When the lease has expired, the client must start over with the DHCP Discover process.
The client ends the lease − DHCPRELEASE.
- The client ends the lease by sending a DHCP Release message to the DHCP server.
- The server will then return the client’s IP address to the available address pool and cancel any remaining lease time.
Source: www.tutorialspoint.com/dynamic-host-configuration-protocol-dhcp
Images Resource: google images.






























 mponent such as a
mponent such as a