[bs_icon name=”glyphicon glyphicon-chevron-right”] The Purpose and Properties of Routing
[bs_icon name=”glyphicon glyphicon-chevron-right”] The Purpose and Properties of Routing
Common IPv4 and IPv6 Routing Protocols
Proper Use of Addressing Technologies
Identify the Following Address Formats
Traceroute – A command-line troubleshooting tool that enables you to view the route to a specified host. This will show how many hops the packets have to travel and how long it takes. In Windows operating systems, the command used is “tracert”.
Here are the steps for troubleshooting a network
CompTIA and Immersive Labs are challenging cybersecurity professionals in the United States and United Kingdom to test their penetration testing skills this month.
The two organizations launched the pen test challenge on the opening day of RSA® Conference 2019.
“Penetration testing, if done right, is a proven and valuable activity that all organizations should engage in,” said Dr. James Stanger, chief technology evangelist at CompTIA. “Unfortunately pen tests are too often done by rote simply to check a box on a compliance form.
“The true value of a pen test occurs when the testers have adequate skills, and when additional security teams use the pen test results to improve procedures and security controls,” Stanger continued. “Our challenge is designed to provide cybersecurity pros with a chance to hone their pen testing skills and have some fun at the same time.”
“It’s great to partner with a such a respected training and global certification provider,” said James Hadley, CEO of Immersive Labs. “We want our gamified and intelligence powered labs to inspire the continuous development of cyber security professionals.”
The CompTIA / Immersive Labs Pen Test Challenge is open to anyone over the age of 18 residing in the U.S. or UK. Visit here to enter the competition and receive a verification email with instructions on how to log in to the Immersive Labs platform to begin the challenge.
Once registered, all participants are automatically entered into a prize drawing. Two winners will be selected by random draw performed by a computer process after the close of the competition on Friday, March 24.
Winners will have their choice of:
The CompTIA Pentest+ Bundle, including CertMaster Learn, a comprehensive, self-paced eLearning program for exam preparation that uses videos, assessment and performance-based questions;
CertMaster Practice, and adaptive knowledge assessment that determines what you’ve already mastered and what you still need to learn to improve confidence and increase retention before taking an exam; and an exam voucher,
or A CompTIA Certification Exam Voucher for the certification of their choice.
Winners will be notified by email. Prizes are non-exchangeable, no-transferable and no cash alternate is offered.
To join the challenge click here.
Be an Ethical Hacker! Check out our CompTIA Security+ certification program. Click here
References: ComTIA Press releases

In this cram guide, we would like to give you some short tips on what to study for the Security+ exam to ensure a great score. Read more »
One of the most essential portions of information security is the design and topology of secure networks. What exactly do we mean by “topology?” Usually, a geographic diagram of a network comes to mind. Read more »
Some of the Security+ exam will test you on your knowledge of some basic email, Internet, and application security issues. Although the amount of detail of knowledge that is required is quite minimal, you must still have a working knowledge of some simple email and application security concepts.
Physical security refers to the aspects of information security that are related to physical threats, such as fire or natural disasters. We will cover some basic physical security threats below: Read more »
Public Key Cryptography is a widely-applied form of cryptography commonly utilized in many network transactions. Read more »
In here we will learn about different symmetric key algorithms and their key features. More importantly, we will learn about some more key concepts related to cryptography as it applies to both symmetric and asymmetric algorithms. Read more »
In subsequent chapters of this study guide, we will take a look at different security topologies or ways that networks can be set up with security in mind. Read more »
A firewall is any hardware or software designed to prevent unwanted network traffic. Some firewalls are simplistic in nature; Read more »
[bs_icon name=”glyphicon glyphicon-chevron-right”] Introduction to Cryptography
Read more »
Despite all the hype about viruses and worms, the Security+ exam actually does not heavily test on viruses and the like. Read more »
One of the most ever-present and ancient uses of the Internet and networking has been to provide remote access to networks or network resources. Read more »
A key aspect to any war is to know your enemy. If you consider the battle against malicious users a war, then understanding the attacks that they use is crucial. Read more »
Incident response [bs_icon name=”glyphicon glyphicon-chevron-right”] Concept and procedures
SNMP: It (SNMP) is a mainstream convention for system administration. It is utilized for gathering data from, and designing, system gadgets, for example, servers, printers, centers, switches, and switches on an Internet Protocol (IP) system. Read more »
A local area network (LAN) is a critical component of a modern data network. A LAN is comprised of one or more computers, a communication protocol, a network topology, and cabling or a wireless network to connect the systems. Read more »
No system or architecture will ever be completely secure; there will always be a certain level of risk. Read more »
Security models of control are used to determine how security will be implemented, what subjects can access the system, and what objects they will have access to. Simply stated, they are a way to formalize security policy. Read more »
Although a robust architecture is a good start, real security requires that you have security mechanisms in place to control processes and applications. Some good security mechanisms are described in the following sections. Read more »
At the core of every computer system is the CPU and hardware that make it run. Read more »
Penetration testing is a series of activities undertaken to identify and exploit security vulnerabilities. Read more »
Single sign-on is an attempt to address a problem that is common for all users and administrators. Read more »
Data access controls are established to control how subjects can access data, what they can access with it, and what they can do with it once accessed. Three primary types of access control are discussed in this section.
The two law systems that form the basis of legal systems in most countries are: Read more »
Source by wikipedia
To Become Cretified For CISSP Please Visit This Link ;
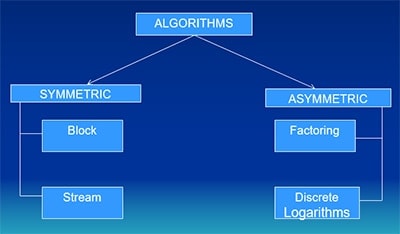
Asymmetric Systems
–Uses a pair of keys (private and public) for encryption and decryption Read more »
Identify Commonly Used TCP/UDP Ports

Common networking command-line tools include the following:
Read more »
An IDS is designed to function as an access-control monitor. It can monitor network or host activity and record which users attempt to access specific network resources. Read more »
Bluetooth is a short-range technology aimed at simplifying communications and synchronization among network devices. Bluetooth is divided into three classes:
Read more »
Wireless Ethernet Versions: (Name – Data Transfer Rate – Frequency) Read more »
Cabling Standards include: Read more »
Networking Protocols include: FTP – File Transfer Protocol : Port 21 Read more »