Power Supplies
Okay, now that we’ve tested our AC outlet and put some protective power devices into play, let’s go ahead and talk power supplies. Read more »

Okay, now that we’ve tested our AC outlet and put some protective power devices into play, let’s go ahead and talk power supplies. Read more »
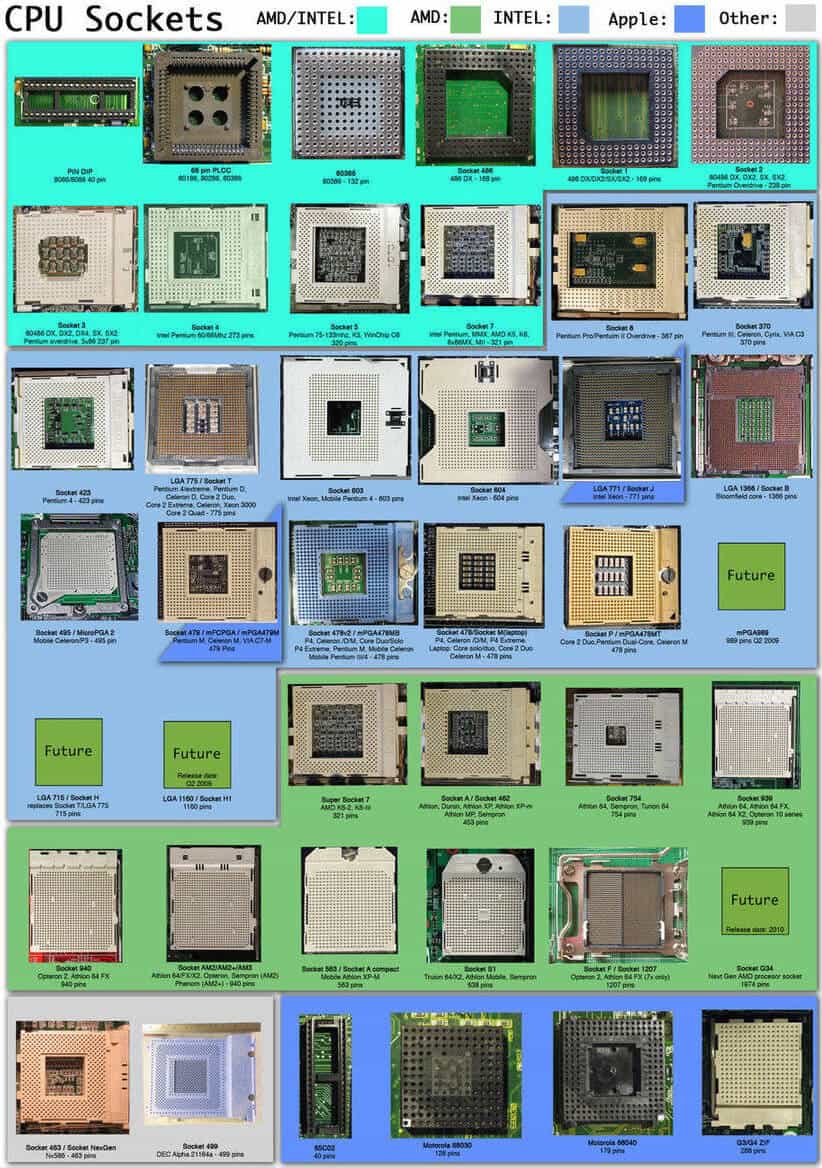
You may not typically handle the insides of your computers, but if your business requires knowledge of Central Processing Units (CPU), then you’ll also need to learn about CPU sockets Read more »
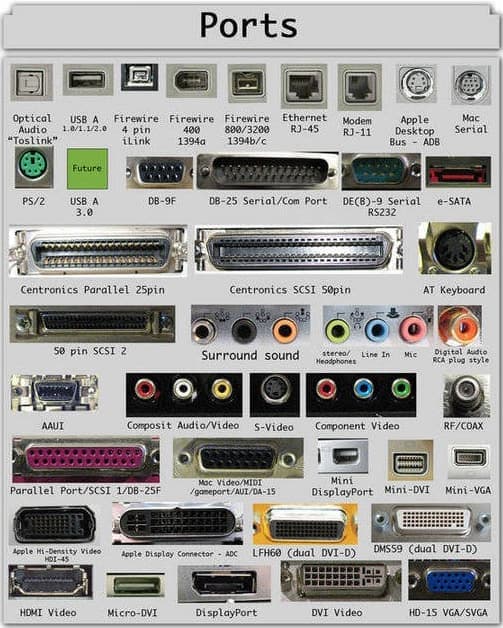
In computer hardware, a port serves as an interface between the computer and other computers or peripheral devices. Read more »
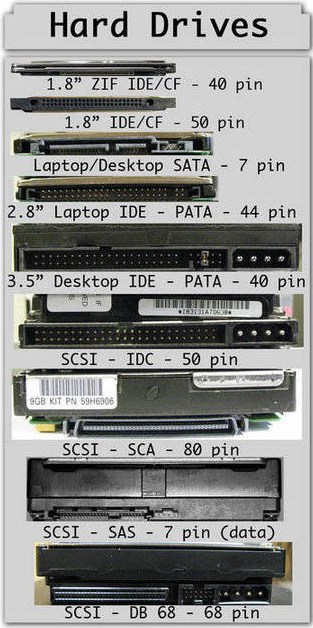
Storage is the hard drive’s responsibility. Everything you keep on your computer is on a hard drive. Read more »
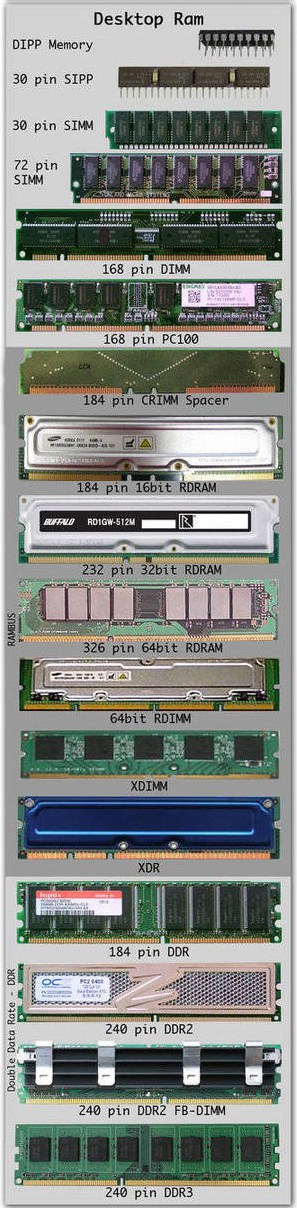
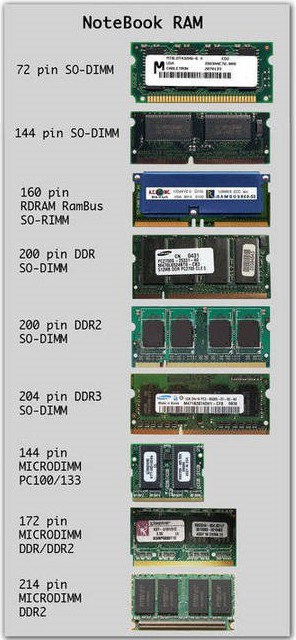
System memory, frequently called main memory or RAM (Random Access Memory), is a type of computer memory that can be accessed randomly. Read more »
Result contains:
Review the BIA
Computer as incidental to other crimes
Tunneling is a method of transferring data from one network to another by encapsulating the packets in an additional header. The additional header provides routing information so that the encapsulating payload traverse the intermediate networks. Read more »
IPSec Encryption: IPSec supports several variations of encryption algorithms, such as, AES.
1.Sending device feeds the original packet and the session key into the encryption formula, calculating the encrypted data.
2.The sending device encapsulates the encrypted data into a packet, which includes the new IP header and VPN header.
3.The sending device sends this new packet to the destination VPN device.
4.The receiving device runs the corresponding decryption formula, the same value as was used by the sending device to decrypt the data.
IPSec KEY Exchange: IPSec uses a dynamic key exchange called Internet Key Exchange (IKE) – defined by RFC 4306. IKE uses a specific process called the Diffie-Hellman (DH) key exchange protocol.
DH allows the devices to make up and exchange key securely.
Internet Key Exchange (IKE)
Security Associations (SAs)
IPSec KEY Authentication and Message Integrity:
Authentication here generally refers to the process by which a receiving VPN device can confirm that a received packet was really sent by a trusted VPN peer.
Message Integrity , sometimes referred to as message authentication, allows the receiver to confirm that the message was not tampered with in transit.
Hashed-based Massage Authentication Code (HMAC) is used. The sending device computes a has and stores the result in the VPN header. The receiving device re-computes the hash using a shared key, and compares the value with the value listed in the VPN header. If it matches then receiver knows message did not change.
| Function | Method | Description |
| Message integrity | HMAC-MD5 | Uses a 128-bit shared key, generating a 128-bit hash value |
| Message integrity | HMAC-SHA | SHA uses different key sizes – 160, 256, 512. Considered better than MD5 but has more overhead. |
| Authentication | Pre-shared Keys | Both VPN devices must be preconfigured with same secret key |
| Authentication | Digital Signatures | RSA is used for encryption.
|
The ESP and AH Security Protocols – IPSec defines these two security protocols with each defining a header.
Encapsulating Security Payload (ESP) – defines the rules for performing authentication, message integrity, encryption and anti-replay. ESP can be used with or without AH.
Authentication Header (AH) – supports authentication and message integrity. AH does not offer any encryption services.
Endpoint communicate with IPSec using either transport or tunnel mode.
To Become Certified For CISSP Please Visit This Link;
Open Systems Interconnect (OSI) Model Read more »
Wide area networks (WANs) are considerably different than LANs. Organizations usually own their own LANs, but WAN services are typically leased; it’s not feasible to have your network guy run a cable from New York to Dallas. Read more »
Measurement plays a critical role within ITIL®, both as a part of Continual Service Improvement, but also within Service Level Management and as an essential part of all processes. Measurements can be used for four basic purposes as shown below: Read more »
Incident Management is concerned with the rapid restoration of services and with minimization of impact to the business. Read more »
The Service Operation phase of the Service Lifecycle is concerned with ensuring that services operate within agreed parameters. When service interruptions do occur, Service Operation is charged with restoring service as quickly as possible and with minimizing the impact to the business.
Service Operation is the only lifecycle phase in which value is actually realized by customers. Whereas all other phases of the Service Lifecycle contribute to and enable value, it is only experienced during Service Operation.
Service Operation also adds business value by:
[bs_icon name=”glyphicon glyphicon-chevron-right”] Balance
Because Service Operation is the first lifecycle phase in which the Service Provider organization must respond to rather than plan for and drive user and customer demand, balance is difficult to maintain. Accordingly, ITIL® emphasizes the importance of striving to achieve and maintain balance during Service Operation in the form of specific balances between :
[bs_icon name=”glyphicon glyphicon-chevron-right”] Communication
During Service Operation, the importance and criticality of communication is especially acute. ITIL stresses the importance of communication :
[bs_icon name=”glyphicon glyphicon-chevron-right”] Incident
An incident is any occurrence which causes or may cause interruption or degradation to an IT Service.
[bs_icon name=”glyphicon glyphicon-chevron-right”] Problem
A problem is the unknown underlying cause of one or more incidents. A problem is NOT just a particularly serious incident.
[bs_icon name=”glyphicon glyphicon-chevron-right”] Error
An error is the known underlying cause of one or more incidents.
[bs_icon name=”glyphicon glyphicon-chevron-right”] Known Error
A known error is the known cause of an incident for which a workaround also exists.
[bs_icon name=”glyphicon glyphicon-chevron-right”] Event
An event is any change of state of an infrastructure or other item which has significance for the delivery of a service.
**Source by wikipedia**
To Become Certified For Exin ITIL Please Visit This Link ;
Change Management is concerned with recording, evaluating, approving, testing, and reviewing changes to services, systems, and other Configuration Items. Read more »
[bs_icon name=”glyphicon glyphicon-chevron-right”] Change Authority
In ITIL® the entity charged with approval of a Request for Change is called the Change Authority. Read more »
IT Security Management is the process concerned with the protection of IT assets (including services) from security threats. Read more »
[bs_icon name=”glyphicon glyphicon-chevron-right”] Normal Changes are changes which meet predefined criteria that qualify them for handling via the Normal Change Management process.
The ‘Four P’s of Service Design’ represent areas which should be taken into consideration when designing a service. Read more »
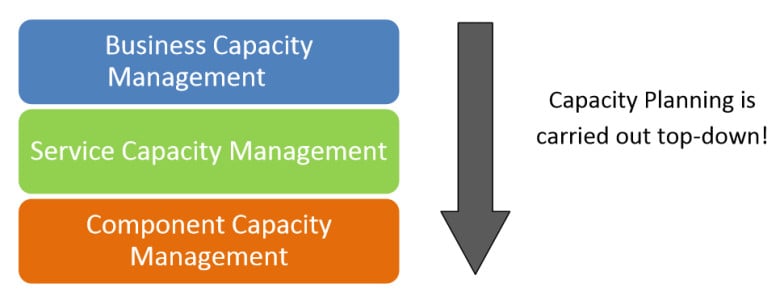
Capacity Management is concerned with ensuring that cost-effective capacity exists at all times which meets or exceeds the agreed needs of the business as established in Service Level Agreements. Read more »
ITIL also utilizes the RACI model as a generic tool for reviewing and assigning four key roles to any important task or activity. Read more »
The Service Desk provides a single point of contact between users and the IT organization.
Source mc mcse Certification Resources
Source mc mcse Certification Resources
Source mc mcse Certification Resources
Source mc mcse Certification Resources

Source mc mcse Certification Resources
Source mc mcse Certification Resources
Crosstalk
Symptoms: Slow network performance and/or an excess of dropped or unintelligible packets. In telephony applications, users hear pieces of voice or conversations from a separate line. Read more »
Source mc mcse Certification Resources
Gather Information on the Problem
In a contact center network, problems are typically discovered and reported by one of the following types of users: Read more »
Source mc mcse Certification Resources

Earlier we built and tested the following topology: Read more »
The Open Systems Interconnection model (OSI model) is a conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system without regard to their underlying internal structure and technology. Read more »
Multilayer Switch – A multilayer switch (MLS) is a computer networking device that switches on OSI layer 2 like an ordinary network switch and provides extra functions on higher OSI layers.
Hub – A physical layer network device used to connect multiple Ethernet devices together. Read more »
Vertical Cross Connect – is a location within a building where cables originate and / or are terminated, reconnected using jumpers or pass throughs or are connected to patch panels or other similar devices where the locations are from upper or lower floors in the building. Read more »
[bs_icon name=”glyphicon glyphicon-chevron-right”] Peer to Peer – A peer to peer network is one in which lacks a dedicated server and every computer acts as both a client and a server. Read more »
Ethernet – Ethernet is the most widely-installed local area network ( LAN) technology. Read more »
[bs_icon name=”glyphicon glyphicon-chevron-right”] Frame Relay – Frame relay is a secure, private network that utilizes a logical path or “virtual circuit” to allocate bandwidth for high performance transmissions. Read more »
568A and 568B – The number 568 refers to the order in which the individual wires inside a CAT 5 cable are terminated. Read more »